In today's rapidly evolving digital landscape, the demand for secure and efficient remote connectivity solutions is at an all-time high. Best remote IoT device SSH has become a cornerstone for organizations aiming to enhance their operational capabilities while maintaining robust security measures. As IoT devices continue to proliferate, understanding how to leverage SSH for remote access is crucial for ensuring seamless connectivity and safeguarding sensitive data.
The increasing reliance on remote work and decentralized operations has pushed businesses to explore advanced solutions for managing IoT devices. Remote IoT device SSH offers a secure channel for administrators to access and manage devices from anywhere in the world, making it an indispensable tool for modern IT infrastructures. With the right strategies and tools in place, organizations can significantly improve their operational efficiency while mitigating potential security risks.
This comprehensive guide will delve into the intricacies of remote IoT device SSH, offering practical insights and actionable tips to help you harness its full potential. Whether you're a seasoned IT professional or a newcomer to the world of IoT, this article will equip you with the knowledge and tools you need to achieve secure and efficient connectivity.
Read also:Hdhub4ucom Your Ultimate Destination For Highquality Movies And Entertainment
Table of Contents:
- Introduction to Remote IoT Device SSH
- Why Remote IoT Device SSH Matters
- How SSH Works for IoT Devices
- Choosing the Best Remote IoT Device SSH Solution
- Key Features of Secure SSH for IoT
- Securing Your IoT SSH Connection
- Common Challenges in Remote IoT Device SSH
- Best Practices for Efficient Remote IoT Device Management
- Real-World Applications of Remote IoT Device SSH
- Future Trends in Remote IoT Device SSH
Introduction to Remote IoT Device SSH
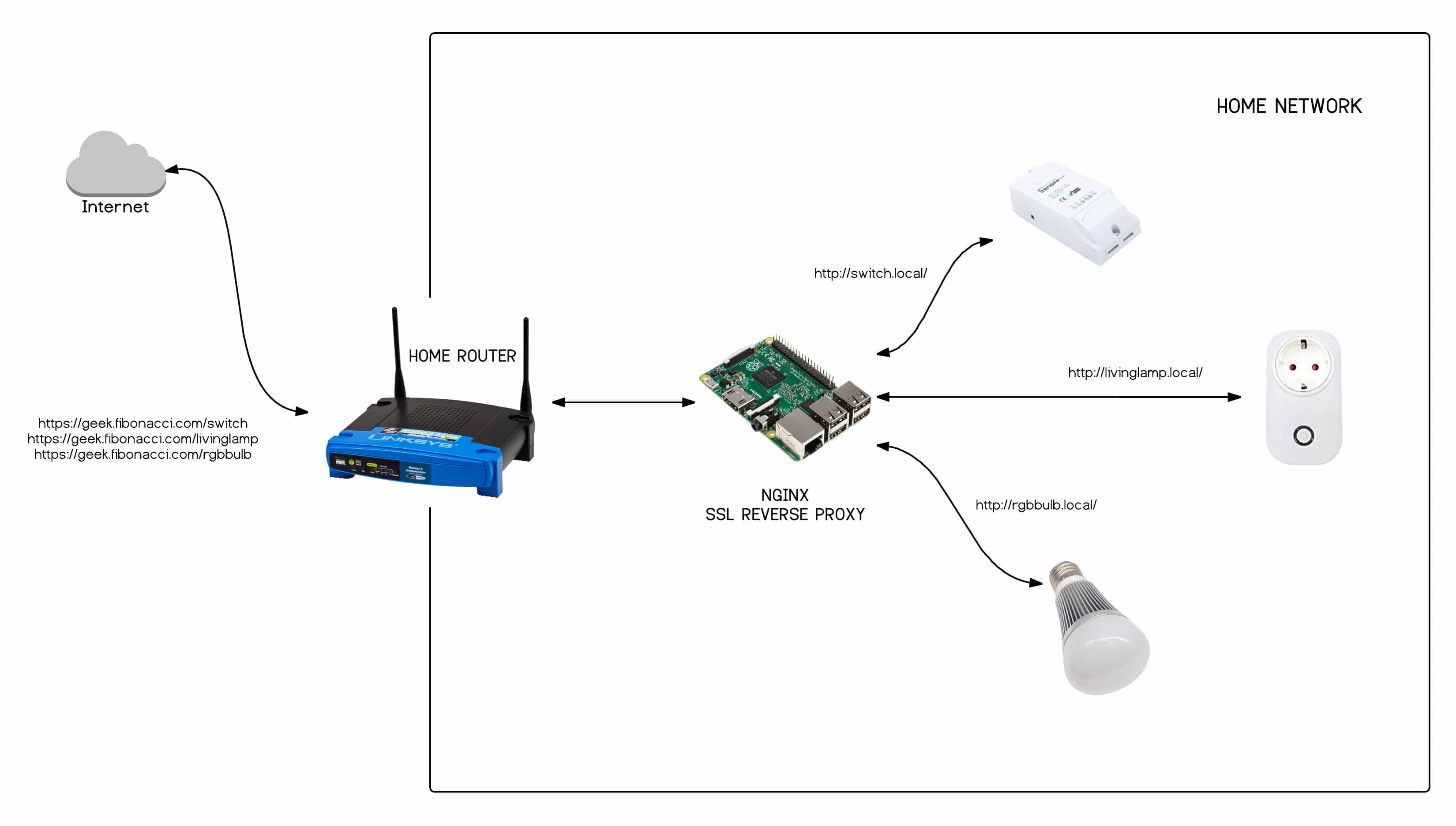
Remote IoT device SSH has revolutionized the way organizations manage their IoT ecosystems. Secure Shell (SSH) is a cryptographic protocol designed to provide secure communication over unsecured networks, making it an ideal solution for remote device management. With SSH, administrators can remotely access IoT devices, execute commands, transfer files, and perform critical maintenance tasks without compromising security.
Understanding SSH Protocol
The SSH protocol operates on a client-server model, where a client initiates a connection to a server running an SSH daemon. This connection is encrypted using strong cryptographic algorithms, ensuring that all data exchanged between the client and server remains confidential and tamper-proof. For IoT devices, SSH provides a reliable and secure means of communication, even in challenging network environments.
Why IoT Needs SSH
IoT devices often operate in diverse and unpredictable environments, making them vulnerable to various security threats. SSH addresses these challenges by offering a secure and encrypted communication channel. By implementing SSH, organizations can protect their IoT devices from unauthorized access, data breaches, and other malicious activities.
Why Remote IoT Device SSH Matters
In an era where IoT devices are becoming increasingly prevalent, the ability to manage them remotely is crucial for maintaining operational efficiency. Remote IoT device SSH allows organizations to streamline their workflows, reduce downtime, and improve overall productivity. By enabling secure remote access, SSH empowers IT teams to address issues promptly and efficiently, regardless of their physical location.
Enhancing Operational Efficiency
With remote IoT device SSH, administrators can perform tasks such as device configuration, firmware updates, and diagnostic checks without the need for physical presence. This not only saves time but also reduces costs associated with on-site maintenance. Additionally, SSH facilitates collaboration among team members by providing a centralized platform for managing IoT devices.
Read also:Why Toby Be A Good Meme Stands Out In Internet Culture
Improving Security Posture
Security is a top priority for any organization deploying IoT devices. Remote IoT device SSH helps mitigate security risks by encrypting all communication between the client and server. Furthermore, SSH supports authentication mechanisms such as public key authentication, adding an extra layer of security to the remote access process.
How SSH Works for IoT Devices
SSH operates by establishing a secure tunnel between the client and server, ensuring that all data transmitted over the network remains confidential and intact. For IoT devices, this means that sensitive information such as device configurations and sensor data can be accessed and managed securely.
Key Components of SSH
- Client-Server Architecture: SSH uses a client-server model to facilitate secure communication.
- Encryption Algorithms: SSH employs strong encryption algorithms to protect data during transmission.
- Authentication Methods: SSH supports various authentication methods, including password-based and public key authentication.
Steps to Establish an SSH Connection
- Install an SSH client on your local machine.
- Ensure that the IoT device is configured to accept SSH connections.
- Initiate the connection by entering the device's IP address and credentials.
- Once connected, you can execute commands and manage the device remotely.
Choosing the Best Remote IoT Device SSH Solution
Selecting the right SSH solution for your IoT devices is critical for achieving optimal performance and security. When evaluating potential solutions, consider factors such as ease of use, scalability, and compatibility with your existing infrastructure.
Factors to Consider
- Security Features: Look for solutions that offer robust encryption and authentication mechanisms.
- Performance: Ensure that the solution can handle large volumes of data and maintain stable connections.
- Support: Choose a provider that offers reliable customer support and regular updates.
Top SSH Solutions for IoT
Some of the leading SSH solutions for IoT devices include OpenSSH, Dropbear SSH, and WolfSSH. Each of these solutions has its own strengths and weaknesses, so it's essential to evaluate them based on your specific requirements.
Key Features of Secure SSH for IoT
A secure SSH solution for IoT devices should possess several key features to ensure optimal performance and security. These features include strong encryption, robust authentication, and comprehensive logging capabilities.
Encryption Standards
Modern SSH solutions utilize advanced encryption standards such as AES and RSA to protect data during transmission. These standards provide a high level of security, making it difficult for attackers to intercept or decipher sensitive information.
Authentication Mechanisms
SSH supports a variety of authentication mechanisms, including password-based, public key, and multi-factor authentication. Public key authentication is particularly popular in IoT environments due to its simplicity and effectiveness.
Securing Your IoT SSH Connection
While SSH provides a secure communication channel, it's essential to implement additional measures to further enhance security. This includes configuring firewalls, limiting access, and regularly updating your SSH software.
Firewall Configuration
Configuring firewalls to restrict access to your SSH server can help prevent unauthorized connections. By limiting access to specific IP addresses or networks, you can significantly reduce the risk of attacks.
Regular Updates
Keeping your SSH software up to date is crucial for addressing security vulnerabilities and ensuring optimal performance. Regular updates often include patches for known issues and improvements to existing features.
Common Challenges in Remote IoT Device SSH
Despite its many advantages, remote IoT device SSH is not without its challenges. Issues such as network latency, limited bandwidth, and outdated software can impact the performance and security of SSH connections.
Overcoming Network Latency
Network latency can cause delays in SSH connections, making it difficult to perform time-sensitive tasks. To mitigate this issue, consider optimizing your network infrastructure and using compression techniques to reduce data transfer times.
Dealing with Limited Bandwidth
In environments with limited bandwidth, SSH connections may become sluggish or unstable. Implementing traffic prioritization and using lightweight SSH clients can help alleviate these issues.
Best Practices for Efficient Remote IoT Device Management
To maximize the benefits of remote IoT device SSH, it's important to follow best practices for efficient device management. These practices include regular monitoring, documentation, and staff training.
Monitoring and Documentation
Regular monitoring of SSH connections can help identify potential issues before they escalate. Maintaining comprehensive documentation of device configurations and access logs is also essential for troubleshooting and auditing purposes.
Staff Training
Ensuring that your IT staff is well-trained in SSH protocols and best practices is crucial for maintaining secure and efficient remote connectivity. Regular training sessions and knowledge sharing can help improve overall proficiency and reduce the likelihood of errors.
Real-World Applications of Remote IoT Device SSH
Remote IoT device SSH has numerous real-world applications across various industries, including healthcare, manufacturing, and transportation. By enabling secure and efficient remote connectivity, SSH helps organizations achieve their operational goals while maintaining robust security measures.
Healthcare
In the healthcare industry, SSH is used to manage medical devices and systems remotely, ensuring that critical data is accessible and secure. This allows healthcare providers to deliver high-quality care while minimizing the risk of data breaches.
Manufacturing
Manufacturing facilities rely on SSH to monitor and control IoT devices used in production processes. By enabling remote access, SSH helps improve efficiency and reduce downtime, ultimately leading to increased productivity.
Future Trends in Remote IoT Device SSH
As the IoT landscape continues to evolve, so too will the technologies and solutions used for remote device management. Emerging trends such as quantum encryption and AI-driven security are poised to transform the way organizations approach SSH for IoT devices.
Quantum Encryption
Quantum encryption offers a new level of security by leveraging the principles of quantum mechanics to protect data. As this technology becomes more widely adopted, it could revolutionize the way SSH is implemented for IoT devices.
AI-Driven Security
AI-driven security solutions are becoming increasingly popular for detecting and mitigating potential threats in real-time. By integrating AI into SSH protocols, organizations can enhance their security posture and improve overall efficiency.
Kesimpulan
Best remote IoT device SSH is an essential tool for organizations seeking to achieve secure and efficient connectivity in their IoT ecosystems. By understanding the principles and best practices of SSH, you can harness its full potential to streamline operations, improve security, and drive innovation. As the IoT landscape continues to evolve, staying informed about the latest trends and technologies will be crucial for maintaining a competitive edge.
We invite you to share your thoughts and experiences with remote IoT device SSH in the comments section below. Additionally, feel free to explore our other articles for more insights into the world of IoT and cybersecurity. Together, let's build a safer and more connected future!