In today's interconnected world, mastering RemoteIoT SSH is becoming an essential skill for IT professionals, IoT enthusiasts, and cybersecurity experts. The ability to securely access and manage IoT devices remotely is crucial for maintaining operational efficiency and data integrity. This guide delves deep into the intricacies of RemoteIoT SSH, including its protocols, best practices, and advanced techniques, ensuring you have a comprehensive understanding of the subject.
Whether you're a beginner or an advanced user, this article provides valuable insights into RemoteIoT SSH. From understanding the basics to implementing advanced configurations, we'll walk you through every step of the process. By the end of this guide, you'll be equipped with the knowledge to enhance your remote IoT management capabilities.
As technology evolves, so does the need for secure and efficient remote access solutions. This guide focuses on the specific protocol RemoteIoT SSH 23252368 2357238123512357236023812341236623462344, providing a complete overview of its functionalities and applications. Let's dive in!
Read also:Why Toby Be A Good Meme Stands Out In Internet Culture
Table of Contents
- Introduction to RemoteIoT SSH
- Understanding RemoteIoT SSH Protocols
- Setting Up RemoteIoT SSH
- Securing Your RemoteIoT SSH Connection
- Advanced Techniques for RemoteIoT SSH
- Troubleshooting Common Issues
- Best Practices for RemoteIoT SSH
- Real-World Applications of RemoteIoT SSH
- Future of RemoteIoT SSH
- Conclusion and Next Steps
Introduction to RemoteIoT SSH
RemoteIoT SSH is a secure protocol designed to facilitate encrypted communication between IoT devices and remote servers. This section provides an overview of the protocol, its importance, and how it fits into the broader IoT ecosystem.
What is RemoteIoT SSH?
RemoteIoT SSH is a variant of the Secure Shell (SSH) protocol tailored specifically for IoT devices. It allows users to securely access and manage IoT devices from remote locations, ensuring data integrity and confidentiality.
Why is RemoteIoT SSH Important?
With the proliferation of IoT devices, secure remote access has become a critical requirement. RemoteIoT SSH addresses this need by providing a robust framework for secure communication, protecting sensitive data from unauthorized access.
Understanding RemoteIoT SSH Protocols
To effectively use RemoteIoT SSH, it's essential to understand the underlying protocols and mechanisms that make it secure and efficient.
Key Features of RemoteIoT SSH
- Encryption: All data transmitted through RemoteIoT SSH is encrypted, ensuring confidentiality.
- Authentication: The protocol uses strong authentication mechanisms to verify the identity of users and devices.
- Integrity: RemoteIoT SSH ensures data integrity by detecting and preventing tampering during transmission.
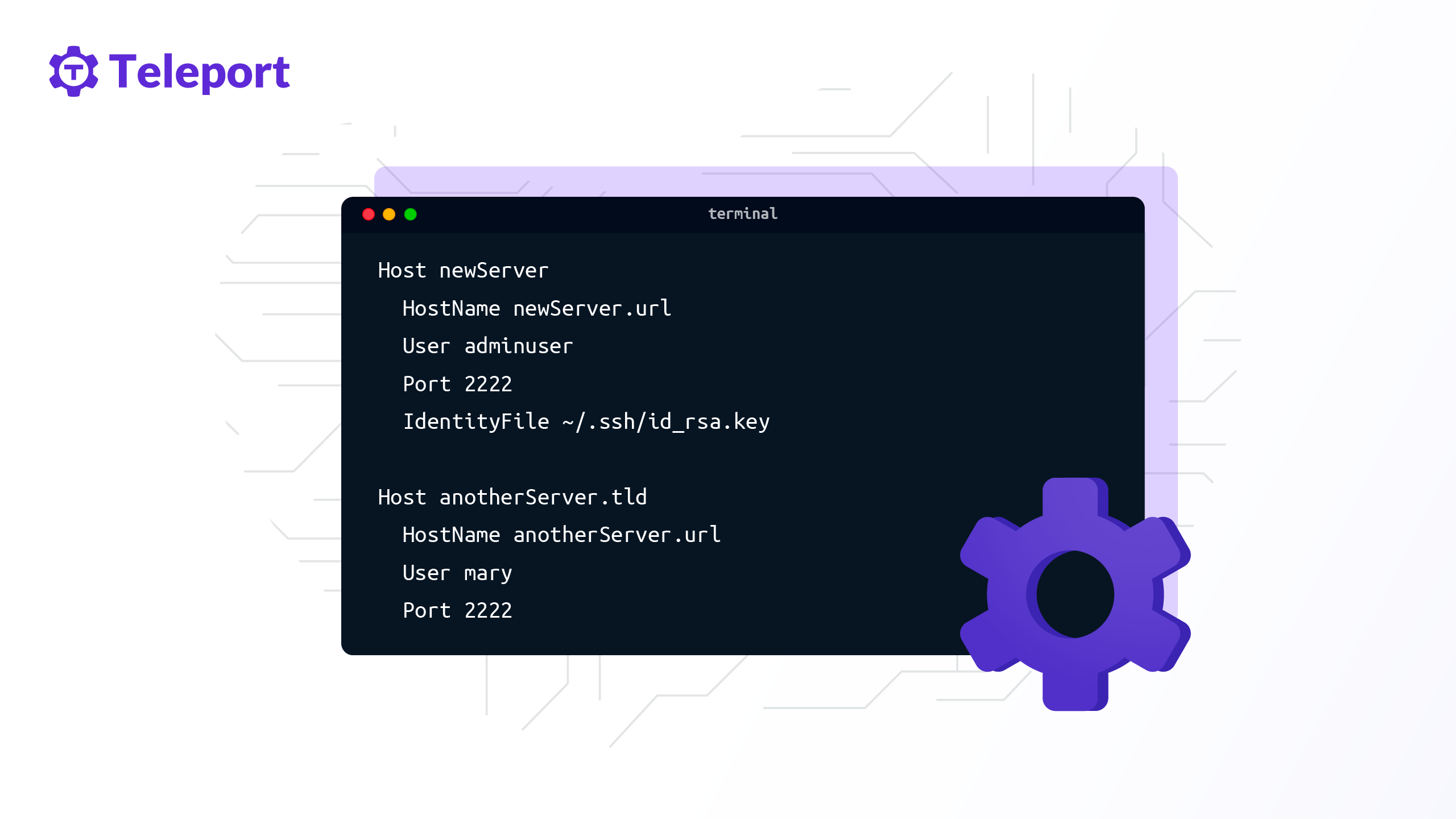
Setting Up RemoteIoT SSH
Setting up RemoteIoT SSH involves several steps, from installing the necessary software to configuring the protocol settings.
Step-by-Step Guide
- Install the RemoteIoT SSH client on your device.
- Configure the server settings to accept RemoteIoT SSH connections.
- Set up user authentication using keys or passwords.
Securing Your RemoteIoT SSH Connection
Security is paramount when using RemoteIoT SSH. This section outlines best practices for securing your connections and protecting sensitive data.
Read also:Hikaru Nagi Sone 385 A Comprehensive Guide To Her Life Career And Impact
Best Security Practices
- Use strong, unique passwords or key-based authentication.
- Regularly update your RemoteIoT SSH software to patch vulnerabilities.
- Monitor connection logs for suspicious activity.
Advanced Techniques for RemoteIoT SSH
For advanced users, RemoteIoT SSH offers a range of features and techniques to enhance its functionality and security.
Port Forwarding
Port forwarding allows you to securely access services running on remote devices through your RemoteIoT SSH connection, enhancing flexibility and control.
Troubleshooting Common Issues
Encountering issues with RemoteIoT SSH? This section provides solutions to common problems and troubleshooting tips.
Connection Errors
Connection errors can arise due to various reasons, such as incorrect configurations or network issues. Ensure all settings are correctly configured and check network connectivity.
Best Practices for RemoteIoT SSH
Adopting best practices ensures optimal performance and security when using RemoteIoT SSH.
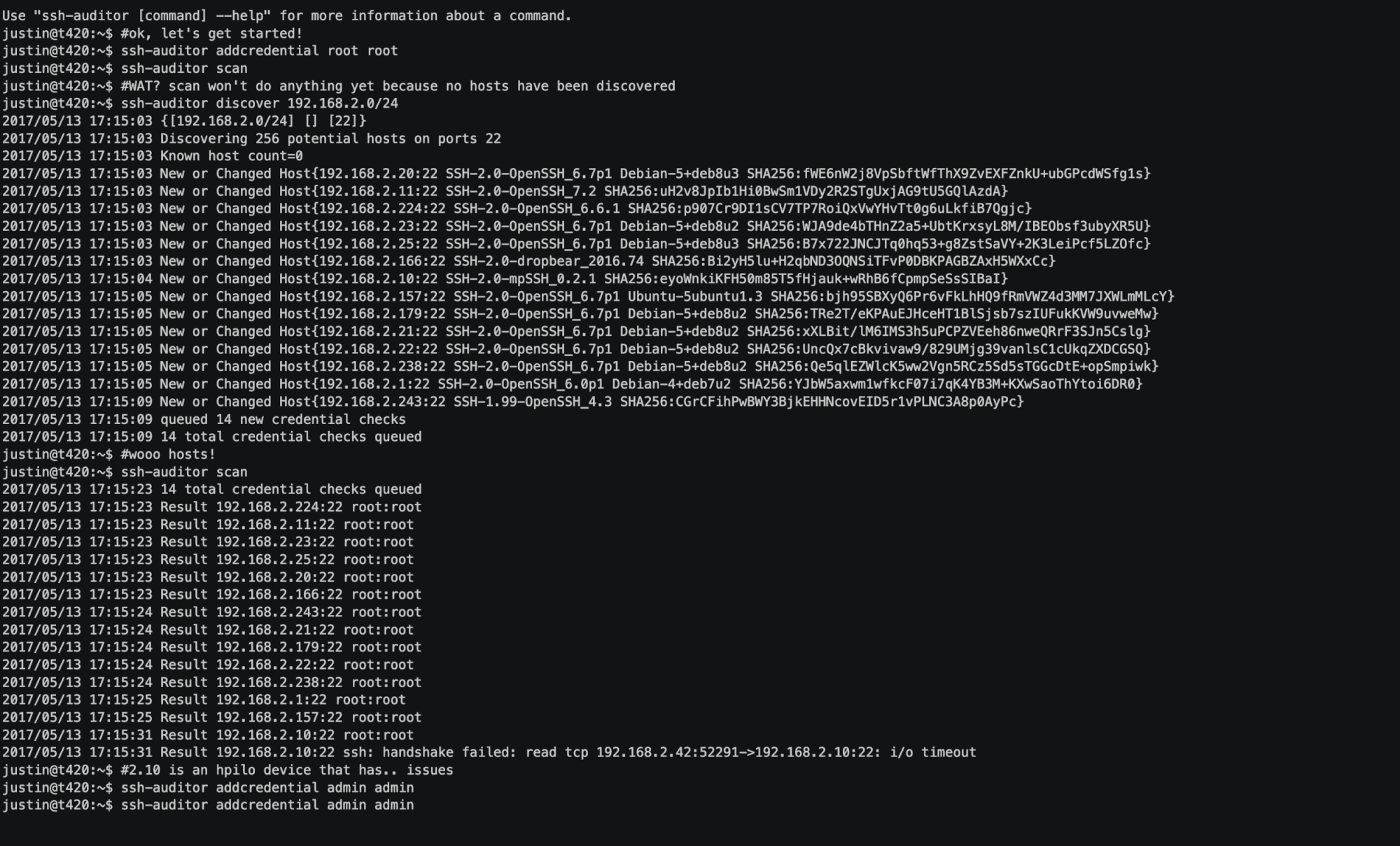
Regular Audits
Conduct regular audits of your RemoteIoT SSH setup to identify and address potential vulnerabilities, ensuring long-term security and reliability.
Real-World Applications of RemoteIoT SSH
RemoteIoT SSH is used in various industries, from manufacturing to healthcare, to manage IoT devices securely and efficiently.
Industrial IoT
In industrial settings, RemoteIoT SSH enables secure remote monitoring and control of critical infrastructure, improving operational efficiency and reducing downtime.
Future of RemoteIoT SSH
As IoT technology continues to evolve, RemoteIoT SSH will play an increasingly important role in securing remote access to devices. Future developments may include enhanced encryption algorithms and more intuitive user interfaces.
Conclusion and Next Steps
Mastering RemoteIoT SSH is essential for anyone working with IoT devices. This guide has provided a comprehensive overview of the protocol, its applications, and best practices for secure implementation.
Take the next step by experimenting with RemoteIoT SSH in your own projects. Share your experiences and insights in the comments below, and explore other articles on our site for further learning.
Data Source: SSH.com, Cisco, NIST.