In today's interconnected world, securely connecting remote IoT devices to a Virtual Private Cloud (VPC) via Raspberry Pi has become a critical need for many tech enthusiasts and professionals alike. As the Internet of Things (IoT) continues to expand, ensuring secure data transmission is paramount. This guide will walk you through the process of securely connecting your IoT devices to a VPC using Raspberry Pi, along with free download options for necessary software and tools.
Whether you're setting up a smart home system, managing industrial sensors, or developing innovative IoT applications, understanding how to secure your IoT devices is essential. This article will cover everything from the basics of IoT security to advanced configurations, ensuring your devices are protected against cyber threats.
By the end of this guide, you'll have a comprehensive understanding of how to connect your Raspberry Pi to a VPC securely, protecting your IoT devices and ensuring smooth operation. Let's dive in and explore the tools, techniques, and best practices to achieve this.
Read also:Unforgettable Chemistry The Dynamic Duo Of Method Man And Redman
Table of Contents:
- Introduction to IoT Security
- Setting Up Raspberry Pi for IoT
- Understanding VPC for IoT
- Steps to Securely Connect IoT Devices
- Free Software Downloads
- Best Practices for IoT Security
- Common Issues and Troubleshooting
- Advanced Configurations for Enhanced Security
- Data Protection Strategies
- Conclusion and Call to Action
Introduction to IoT Security
As the Internet of Things (IoT) continues to grow, the importance of securing these devices cannot be overstated. IoT devices are often deployed in remote locations, making them vulnerable to unauthorized access and cyberattacks. A secure connection is essential to protect sensitive data and maintain the integrity of your network.
Why IoT Security Matters
IoT security is crucial because these devices often handle sensitive information, such as personal data, financial transactions, and critical infrastructure control. A breach in one device can compromise the entire network, leading to significant financial losses and reputational damage.
- Protects against unauthorized access
- Ensures data integrity
- Prevents cyberattacks
- Maintains network stability
Setting Up Raspberry Pi for IoT
The Raspberry Pi is a versatile and affordable single-board computer that can be used as a gateway for IoT devices. Setting it up properly is the first step in creating a secure connection to your VPC.
Steps to Set Up Raspberry Pi
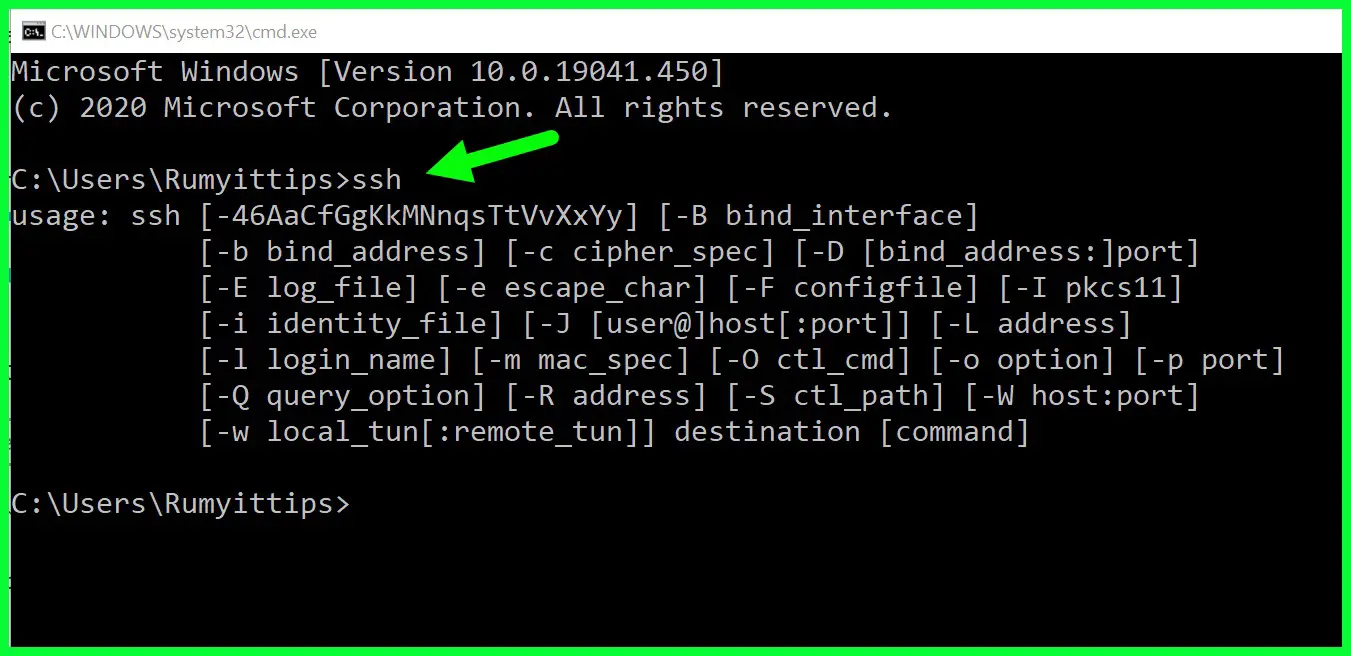
Here’s how you can configure your Raspberry Pi for IoT applications:
- Install the latest version of Raspberry Pi OS.
- Enable SSH for remote access.
- Configure Wi-Fi or Ethernet for internet connectivity.
- Update the system with the latest security patches.
Understanding VPC for IoT
A Virtual Private Cloud (VPC) provides a secure and isolated environment for your IoT devices. It allows you to control access to your devices and manage data flow effectively.
Read also:Discovering Rapid City A Complete Guide To Its Location Attractions And Charm
Key Features of VPC
- Private subnets for device isolation
- Customizable security groups
- Network access control lists (ACLs)
- Integration with cloud services
Steps to Securely Connect IoT Devices
Securing the connection between your IoT devices and the VPC involves several steps. Here’s a detailed guide:
Step 1: Configure Network Settings
Ensure your Raspberry Pi is connected to the correct network and has the necessary permissions to access the VPC.
Step 2: Implement Encryption
Use encryption protocols such as TLS or SSL to secure data transmission between devices and the VPC.
Step 3: Monitor and Audit
Regularly monitor your network for suspicious activities and audit access logs to identify potential threats.
Free Software Downloads
There are several free software tools available to help you securely connect your IoT devices to a VPC via Raspberry Pi. Here are some recommendations:
- OpenVPN: A popular open-source solution for creating secure tunnels.
- WireGuard: A modern and lightweight VPN solution.
- Mosquitto: An open-source MQTT broker for IoT communication.
You can download these tools from their official websites or popular repositories such as GitHub.
Best Practices for IoT Security
Adopting best practices is essential to maintaining a secure IoT environment. Here are some tips:
- Use strong passwords and enable two-factor authentication.
- Regularly update firmware and software.
- Limit access to critical devices and data.
- Monitor network traffic for unusual patterns.
Common Issues and Troubleshooting
Even with proper setup, issues can arise. Here are some common problems and their solutions:
Issue 1: Connectivity Problems
Solution: Check network settings and ensure all devices are properly configured.
Issue 2: Security Alerts
Solution: Review security logs and update firewall rules as needed.
Advanced Configurations for Enhanced Security
For those seeking additional security, advanced configurations can further protect your IoT devices:
Implementing Firewalls
Use firewalls to control incoming and outgoing traffic, ensuring only authorized devices can access your network.
Using Intrusion Detection Systems
Deploy intrusion detection systems (IDS) to monitor for potential threats and take corrective actions automatically.
Data Protection Strategies
Protecting sensitive data is a critical aspect of IoT security. Here are some strategies:
Data Encryption
Encrypt all data both at rest and in transit to prevent unauthorized access.
Access Control
Implement strict access controls to ensure only authorized personnel can access sensitive information.
Conclusion and Call to Action
In conclusion, securely connecting remote IoT devices to a VPC via Raspberry Pi is essential for maintaining a robust and secure network. By following the steps outlined in this guide, you can protect your devices and ensure smooth operation. Remember to regularly update your systems and adopt best practices to stay ahead of potential threats.
We invite you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site for more insights into IoT security and related topics. Together, let's build a safer and more connected world!