Secure Shell (SSH) has become an indispensable protocol for managing IoT networks, especially on Windows systems. As the Internet of Things (IoT) continues to expand, ensuring secure communication between devices is paramount. SSH provides a robust framework to protect data integrity and confidentiality in IoT environments.
In today's interconnected world, IoT networks are growing exponentially, with billions of devices connected globally. However, this rapid expansion also brings significant security challenges. Understanding SSH and its role in IoT networks is crucial for safeguarding sensitive data and maintaining operational efficiency.
This article dives deep into the intricacies of Secure Shell (SSH) in IoT networks, focusing specifically on its implementation and management on Windows platforms. By the end, you'll have a comprehensive understanding of how SSH works, its applications, and best practices to secure your IoT infrastructure.
Read also:Discovering Rapid City A Complete Guide To Its Location Attractions And Charm
Table of Contents
- Introduction to Secure Shell (SSH)
- The Role of SSH in IoT Networks
- Implementing SSH on Windows
- Benefits of Using SSH in IoT Networks
- Security Considerations for SSH in IoT
- Common SSH Commands for IoT Devices
- Understanding SSH Encryption Mechanisms
- Troubleshooting SSH Connections in IoT Networks
- Best Practices for Securing SSH in IoT Networks
- Future Trends in SSH and IoT Integration
- Conclusion and Call to Action
Introduction to Secure Shell (SSH)
Secure Shell (SSH) is a cryptographic network protocol designed for secure data communication over unsecured networks. Initially developed in 1995 by Tatu Ylönen, SSH has evolved into a cornerstone of modern cybersecurity practices. It provides a secure channel for remote access, file transfer, and command execution between devices.
SSH operates on port 22 by default and uses public-key cryptography to authenticate clients and servers. This ensures that only authorized users can access the network while protecting data from eavesdropping and tampering. Understanding SSH is essential for anyone managing IoT networks, especially on Windows systems where secure communication is critical.
In the context of IoT, SSH offers a reliable solution for managing devices remotely, updating firmware, and monitoring network activity. Its robust encryption and authentication mechanisms make it an ideal choice for securing IoT networks against potential threats.
The Role of SSH in IoT Networks
Enhancing Security in IoT
IoT networks consist of numerous interconnected devices, each with its own vulnerabilities. SSH plays a pivotal role in securing these devices by providing encrypted communication channels. By using SSH, administrators can remotely manage IoT devices without compromising security.
Some key benefits of SSH in IoT networks include:
- End-to-end encryption for data transmission
- Strong authentication mechanisms to prevent unauthorized access
- Support for secure file transfers using SFTP (SSH File Transfer Protocol)
SSH as a Gateway for IoT Management
SSH serves as a gateway for managing IoT devices, enabling administrators to execute commands, transfer files, and monitor device performance. This is particularly useful in large-scale IoT deployments where manual management is impractical.
Read also:A Comprehensive Guide To The Sagittarius Personality Uncover Their Traits And Characteristics
For example, SSH allows administrators to:
- Update device firmware remotely
- Monitor network activity in real-time
- Diagnose and resolve issues without physical access to the device
Implementing SSH on Windows
Enabling SSH on Windows
Windows 10 and later versions come with built-in SSH client and server functionality. To enable SSH on Windows, follow these steps:
- Open the "Turn Windows features on or off" settings
- Check the box for "OpenSSH Client" and "OpenSSH Server"
- Restart your system to apply the changes
Once enabled, you can use the SSH client to connect to remote devices or configure the SSH server to allow incoming connections.
Configuring SSH Server Settings
After enabling the SSH server, you may need to configure additional settings to enhance security. This includes:
- Changing the default port (22) to a custom port
- Disabling password authentication in favor of public-key authentication
- Limiting access to specific IP addresses or user groups
These configurations can be done by editing the SSH server configuration file located at C:\ProgramData\ssh\sshd_config.
Benefits of Using SSH in IoT Networks
Using SSH in IoT networks offers several advantages, including:
- Security: SSH encrypts all data transmitted between devices, protecting it from interception and tampering.
- Reliability: SSH ensures that commands and files are transmitted accurately, reducing the risk of errors.
- Scalability: SSH can handle large-scale IoT deployments, making it suitable for enterprise-level networks.
- Interoperability: SSH is compatible with a wide range of devices and operating systems, including Windows, Linux, and macOS.
These benefits make SSH an essential tool for managing IoT networks securely and efficiently.
Security Considerations for SSH in IoT
Common Vulnerabilities in SSH
While SSH is a secure protocol, it is not immune to vulnerabilities. Some common threats include:
- Brute-force attacks targeting weak passwords
- Man-in-the-middle attacks exploiting weak key exchange algorithms
- Configuration errors leading to unauthorized access
To mitigate these risks, it is essential to implement strong security measures, such as using public-key authentication and regularly updating SSH software.
Best Practices for Securing SSH
Here are some best practices for securing SSH in IoT networks:
- Use strong, unique passwords or public-key authentication
- Disable root login to prevent unauthorized access
- Monitor SSH logs for suspicious activity
- Regularly update SSH software to patch known vulnerabilities
Common SSH Commands for IoT Devices
SSH provides a wide range of commands for managing IoT devices. Some commonly used commands include:
ssh user@hostname– Connect to a remote devicescp file user@hostname:/path– Transfer files securelyssh-keygen– Generate public and private keys for authenticationssh-copy-id user@hostname– Copy public key to a remote device
These commands enable administrators to perform various tasks, such as connecting to devices, transferring files, and managing keys securely.
Understanding SSH Encryption Mechanisms
How SSH Encryption Works
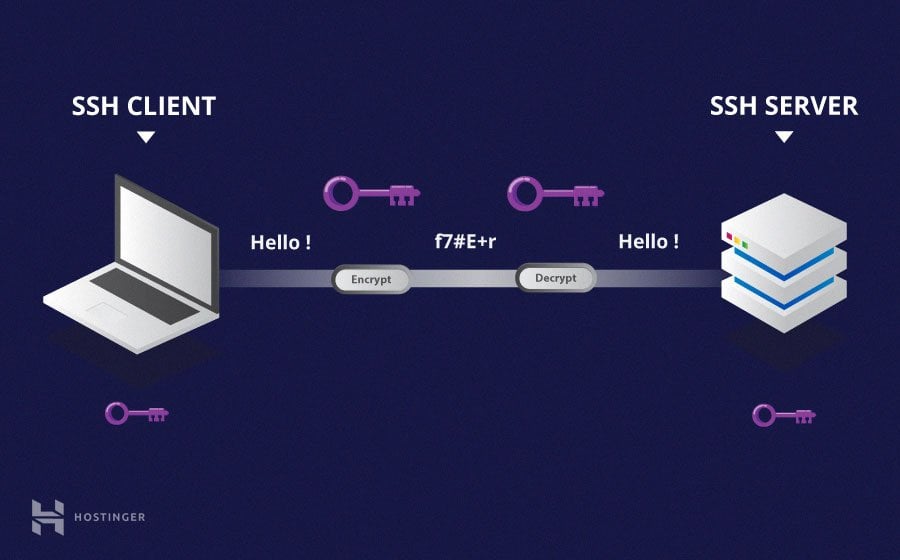
SSH uses a combination of symmetric and asymmetric encryption to secure data transmission. During the initial connection, SSH establishes a secure channel using public-key cryptography. Once the channel is established, symmetric encryption is used for faster data transfer.
The encryption algorithms supported by SSH include:
- AES (Advanced Encryption Standard)
- ChaCha20
- Blowfish
These algorithms ensure that data is transmitted securely and cannot be intercepted by unauthorized parties.
Key Exchange Algorithms
SSH uses key exchange algorithms to establish a secure connection between devices. Some commonly used algorithms include:
- Diffie-Hellman
- ECDH (Elliptic Curve Diffie-Hellman)
- Curve25519
These algorithms ensure that the encryption keys are securely exchanged without exposing them to potential attackers.
Troubleshooting SSH Connections in IoT Networks
Despite its robustness, SSH connections can sometimes fail due to various reasons. Here are some common issues and their solutions:
- Connection Refused: Ensure that the SSH server is running and the port is open.
- Authentication Failure: Verify that the username and password are correct or that the public key is properly configured.
- Timeout Errors: Check network connectivity and firewall settings.
If the issue persists, consult the SSH logs for more detailed information. These logs can provide valuable insights into the root cause of the problem.
Best Practices for Securing SSH in IoT Networks
To ensure the security of SSH in IoT networks, follow these best practices:
- Use strong, unique passwords or public-key authentication
- Disable root login and create separate user accounts for administrative tasks
- Regularly update SSH software to patch known vulnerabilities
- Monitor SSH logs for suspicious activity and implement intrusion detection systems
- Limit access to trusted IP addresses or user groups
By implementing these practices, you can significantly enhance the security of your IoT network and protect it from potential threats.
Future Trends in SSH and IoT Integration
As IoT continues to evolve, the role of SSH in securing IoT networks will become even more critical. Future trends in SSH and IoT integration include:
- Quantum-resistant encryption algorithms to protect against future quantum computing threats
- AI-driven monitoring systems to detect and respond to security threats in real-time
- Integration with blockchain technology for decentralized authentication and data integrity
These advancements will further enhance the security and reliability of SSH in IoT networks, ensuring that devices remain protected as the IoT ecosystem continues to grow.
Conclusion and Call to Action
In conclusion, understanding Secure Shell (SSH) and its role in IoT networks is essential for maintaining secure and efficient communication between devices. By implementing SSH on Windows systems and following best practices for security, administrators can protect their IoT networks from potential threats.
We encourage readers to take action by enabling SSH on their Windows systems, configuring secure settings, and regularly updating their software. Additionally, we invite you to share your thoughts and experiences in the comments section below or explore other articles on our site for more insights into IoT security.