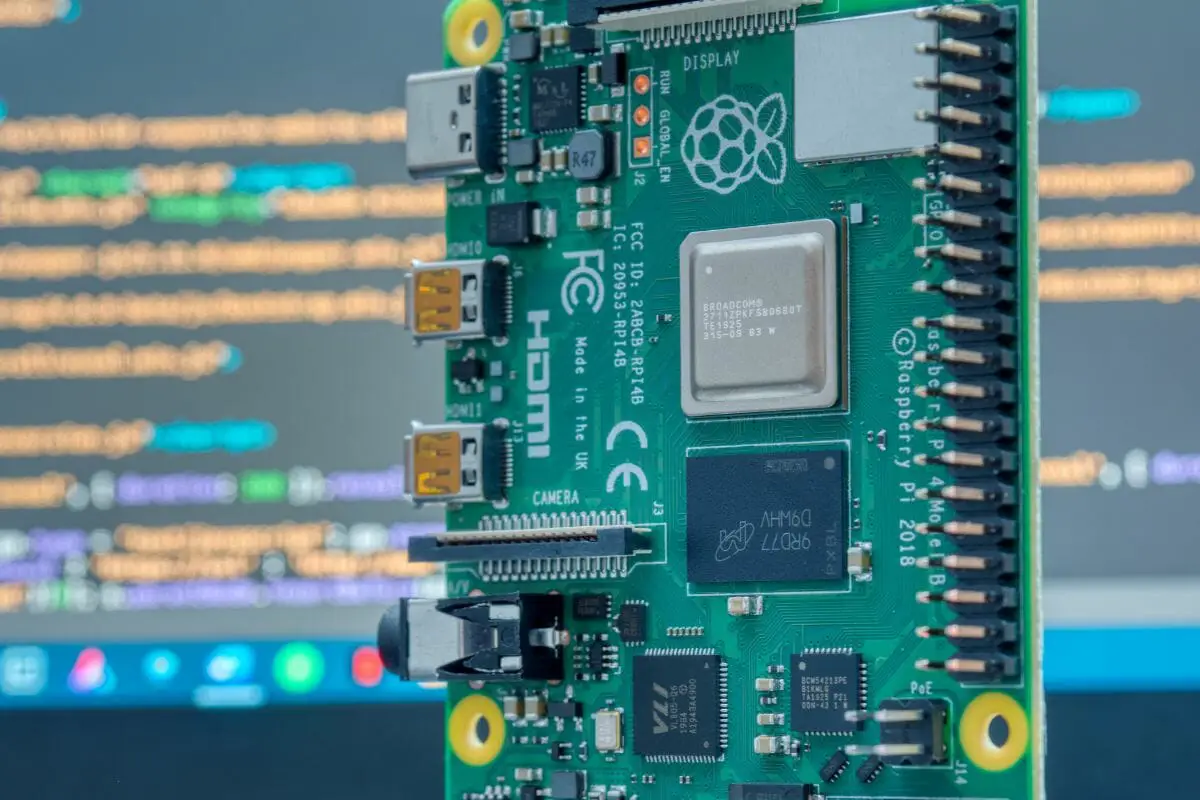
Accessing your Raspberry Pi securely over the internet is a common need for many tech enthusiasts and professionals. However, when your Raspberry Pi is behind a firewall, this task becomes more challenging. In this article, we will explore how to SSH into your Raspberry Pi behind a firewall without relying on free download tools, ensuring secure and reliable connectivity.
SSH (Secure Shell) is an essential tool for remote management of devices like Raspberry Pi. Whether you're managing servers, automating processes, or running IoT applications, being able to SSH into your Raspberry Pi remotely is critical. However, firewalls often block direct access, making it necessary to explore alternative methods.
This guide will walk you through the process step-by-step, ensuring you understand the technical aspects and best practices for maintaining security while enabling remote access. By the end of this article, you'll have the knowledge and tools to configure your Raspberry Pi for remote SSH access behind a firewall.
Read also:Haiden Deegan Dad A Comprehensive Look Into The Life And Legacy Of A Motocross Legend
Table of Contents
- Introduction
- Understanding Firewalls and Their Impact
- Setting Up SSH on Raspberry Pi
- Port Forwarding: The Basics
- Dynamic DNS Solutions
- Using SSH Tunnels for Secure Access
- Cloud-Based Solutions for Remote Access
- Security Best Practices for SSH
- Troubleshooting Common Issues
- Conclusion
Introduction
SSH to Raspberry Pi behind firewall without free download tools is a practical solution for tech-savvy individuals who need remote access to their devices. In today's interconnected world, managing remote devices securely and efficiently is crucial. Firewalls, while essential for security, can sometimes hinder this process. This guide aims to provide you with a comprehensive understanding of how to overcome these challenges.
Whether you're a beginner or an advanced user, this article will cover everything you need to know about configuring SSH for your Raspberry Pi. From setting up the initial SSH service to implementing advanced techniques like SSH tunnels and cloud-based solutions, we'll ensure you have the tools to succeed.
By the end of this guide, you'll be equipped with the knowledge to securely access your Raspberry Pi remotely, even when it's behind a restrictive firewall.
Understanding Firewalls and Their Impact
Firewalls are security systems designed to monitor and control incoming and outgoing network traffic based on predetermined security rules. They play a vital role in protecting devices and networks from unauthorized access and potential threats. However, firewalls can also block legitimate traffic, such as SSH connections, if not configured correctly.
Types of Firewalls
- Network Firewalls: These firewalls protect an entire network by filtering traffic at the perimeter.
- Host-Based Firewalls: Installed on individual devices, these firewalls provide an additional layer of security.
Understanding the type of firewall protecting your Raspberry Pi is essential for configuring remote access. Network firewalls often require port forwarding or dynamic DNS setup, while host-based firewalls may need specific rules to allow SSH traffic.
Setting Up SSH on Raspberry Pi
Before attempting to SSH into your Raspberry Pi, ensure that the SSH service is properly configured and running. Here's a step-by-step guide to setting up SSH on your Raspberry Pi:
Read also:Who Is Joan Drummond Mcgowan Unveiling The Life And Legacy
Step 1: Enable SSH on Raspberry Pi
To enable SSH on your Raspberry Pi, follow these steps:
- Connect your Raspberry Pi to a monitor and keyboard.
- Open the terminal and type `sudo raspi-config`.
- Select "Interfacing Options" and then "SSH".
- Choose "Yes" to enable SSH and confirm your choice.
Step 2: Check SSH Status
Once enabled, verify that the SSH service is running by typing `sudo systemctl status ssh` in the terminal. If the service is active, you're ready to proceed.
Port Forwarding: The Basics
Port forwarding is a technique used to direct incoming traffic from the internet to a specific device on your local network. It's a common method for enabling remote SSH access to a Raspberry Pi behind a firewall.
How to Set Up Port Forwarding
Follow these steps to set up port forwarding on your router:
- Log in to your router's admin interface using its IP address.
- Navigate to the "Port Forwarding" or "NAT" settings.
- Create a new rule, specifying the external port (e.g., 22 for SSH) and the internal IP address of your Raspberry Pi.
- Save the settings and restart your router if necessary.
By configuring port forwarding, you allow your Raspberry Pi to receive SSH connections from the internet.
Dynamic DNS Solutions
If your internet service provider assigns a dynamic IP address, maintaining a stable connection to your Raspberry Pi can be challenging. Dynamic DNS (DDNS) services provide a solution by mapping your dynamic IP to a static domain name.
Popular DDNS Services
- No-IP
- Dynu
- duckdns
These services offer free and paid plans, allowing you to configure your Raspberry Pi to update its IP address automatically. This ensures that you can always reach your device using a consistent domain name.
Using SSH Tunnels for Secure Access
SSH tunnels provide an encrypted connection between your local machine and the Raspberry Pi, bypassing firewall restrictions. This method is particularly useful when direct access is not possible.
Setting Up an SSH Tunnel
Follow these steps to create an SSH tunnel:
- Install an SSH client on your local machine (e.g., PuTTY for Windows or OpenSSH for Linux/Mac).
- Use the command `ssh -R 2222:localhost:22 user@remote_server` to create a reverse tunnel.
- Access your Raspberry Pi by connecting to `localhost:2222` from the remote server.
SSH tunnels ensure that your connection remains secure and private, even when traversing untrusted networks.
Cloud-Based Solutions for Remote Access
Cloud-based solutions offer an alternative to traditional SSH methods by providing a centralized platform for managing remote devices. Services like ngrok and Serveo enable you to expose your Raspberry Pi to the internet without modifying your firewall settings.
Advantages of Cloud-Based Solutions
- Easy setup and configuration
- Support for multiple protocols
- Reliable and secure connections
These services are especially useful for users who lack administrative access to their network or prefer a hands-off approach to remote access.
Security Best Practices for SSH
When configuring SSH for remote access, it's essential to follow security best practices to protect your Raspberry Pi from unauthorized access.
Best Practices
- Use strong, unique passwords or SSH keys for authentication.
- Disable password authentication and rely solely on SSH keys.
- Change the default SSH port to a non-standard value.
- Limit SSH access to specific IP addresses or ranges.
- Regularly update your Raspberry Pi's operating system and software.
Implementing these practices will significantly enhance the security of your SSH setup and protect your device from potential threats.
Troubleshooting Common Issues
Despite careful configuration, issues may arise when setting up SSH access to your Raspberry Pi. Here are some common problems and their solutions:
Problem: Unable to Connect via SSH
- Ensure that the SSH service is running on your Raspberry Pi.
- Verify that port forwarding is correctly configured on your router.
- Check your firewall settings to ensure they allow SSH traffic.
Problem: Connection Timeout
- Confirm that your Raspberry Pi's IP address is correct.
- Test the connection using a different network or device.
- Restart your router and Raspberry Pi to reset the connection.
By addressing these issues systematically, you can resolve most connectivity problems and ensure smooth SSH access to your Raspberry Pi.
Conclusion
SSH to Raspberry Pi behind firewall without free download tools is a practical and secure way to manage your devices remotely. By understanding firewalls, configuring SSH properly, and implementing advanced techniques like SSH tunnels and cloud-based solutions, you can overcome common challenges and maintain reliable access.
We encourage you to experiment with the methods outlined in this guide and share your experiences in the comments below. For more information on Raspberry Pi and SSH, explore our other articles or reach out to our community for support. Together, let's make remote device management easier and more secure!