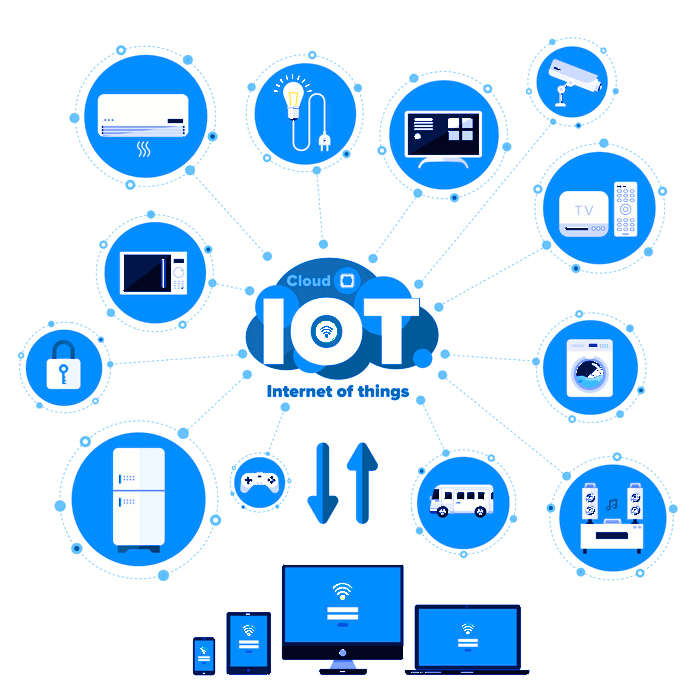
In today's digital era, the Internet of Things (IoT) has revolutionized the way we interact with technology. From smart homes to industrial automation, IoT devices have become an integral part of our daily lives. However, securing these devices remains a critical challenge. One of the most reliable methods to enhance IoT security is through SSH (Secure Shell) access. If you're looking for SSH IoT device free download options, you've come to the right place.
As the number of connected devices continues to grow exponentially, so does the risk of cyber threats. Hackers are constantly seeking vulnerabilities in IoT systems, making it crucial for users to implement robust security measures. SSH provides encrypted communication between devices, ensuring that your data remains safe from unauthorized access.
This comprehensive guide will walk you through everything you need to know about securing IoT devices with SSH, including how to obtain free SSH IoT device downloads, best practices for implementation, and expert tips for maintaining optimal security. Whether you're a beginner or an advanced user, this article will equip you with the knowledge to protect your IoT ecosystem effectively.
Read also:Jey Uso Children A Closer Look At His Family Life
Table of Contents
- Introduction to SSH
- Why Secure IoT with SSH?
- Types of SSH Clients
- How to Download SSH for IoT Devices
- Installation Process
- Best Practices for SSH Implementation
- Common SSH Issues and Solutions
- Security Tips for IoT Devices
- Real-World Examples of SSH in IoT
- Conclusion
Introduction to SSH
SSH, or Secure Shell, is a cryptographic network protocol designed to provide secure communication over an unsecured network. It is widely used for remote administration and file transfer between devices. In the context of IoT, SSH plays a vital role in securing communications between IoT devices and servers.
SSH ensures data integrity, confidentiality, and authentication, making it an essential tool for protecting sensitive information. By encrypting data during transmission, SSH prevents unauthorized access and eavesdropping, reducing the risk of cyberattacks.
Advantages of Using SSH
- Encryption of data during transmission
- Strong authentication mechanisms
- Protection against man-in-the-middle attacks
- Compatibility with various operating systems
Why Secure IoT with SSH?
IoT devices are often targeted by hackers due to their widespread deployment and potential vulnerabilities. Without proper security measures, these devices can be easily compromised, leading to data breaches, financial losses, and even physical harm in some cases.
By implementing SSH, you can significantly enhance the security of your IoT devices. SSH offers a secure channel for communication, ensuring that only authorized users can access your devices. This is particularly important for devices that handle sensitive data, such as smart home systems, medical devices, and industrial automation equipment.
Types of SSH Clients
There are several SSH clients available, each catering to different user needs and preferences. Some popular options include:
1. PuTTY
PuTTY is a free and open-source SSH client widely used for Windows systems. It offers a simple interface and supports various protocols, including SSH, Telnet, and Serial.
Read also:Ellaalexandraxo Nude Content Understanding The Phenomenon And Its Impact
2. OpenSSH
OpenSSH is a widely-used SSH client for Unix-based systems, including Linux and macOS. It is known for its robust security features and ease of use.
3. Bitvise SSH Client
Bitvise SSH Client is a powerful tool for Windows users, offering advanced features such as SFTP file transfer and terminal emulation.
How to Download SSH for IoT Devices
Obtaining SSH for IoT devices can be done through various channels, depending on your specific requirements. Below are some free download options:
1. OpenSSH for IoT
OpenSSH is a popular choice for securing IoT devices. You can download it from the official OpenSSH website or through package managers like APT (Advanced Package Tool) for Linux-based systems.
2. SSH Clients for Embedded Systems
For embedded IoT devices, lightweight SSH clients such as Dropbear and WolfSSH are excellent options. These clients are optimized for resource-constrained environments and provide robust security features.
Installation Process
Installing SSH on IoT devices involves a few straightforward steps. Below is a general guide to help you get started:
- Choose the Right SSH Client: Select an SSH client that suits your device's operating system and requirements.
- Download the Client: Obtain the SSH client from a trusted source, such as the official website or a reputable repository.
- Install the Client: Follow the installation instructions provided by the client's documentation. For Linux systems, you can use commands like
sudo apt-get install openssh-server. - Configure SSH Settings: Customize SSH settings to meet your security needs, such as disabling password authentication and enabling public key authentication.
- Test the Connection: Verify that SSH is functioning correctly by establishing a secure connection to your IoT device.
Best Practices for SSH Implementation
To ensure optimal security when using SSH for IoT devices, follow these best practices:
1. Use Strong Passwords
Avoid using weak or default passwords. Instead, opt for strong, complex passwords that include a mix of letters, numbers, and special characters.
2. Enable Public Key Authentication
Public key authentication enhances security by eliminating the need for password-based logins. Generate a public-private key pair and configure your SSH server to accept public keys.
3. Disable Root Login
Restricting root login access reduces the risk of unauthorized access to your IoT devices. Modify the SSH configuration file (sshd_config) to disable root login.
4. Regularly Update SSH Software
Keep your SSH software up to date to ensure that you have the latest security patches and features. Regular updates help protect against newly discovered vulnerabilities.
Common SSH Issues and Solutions
While SSH is a powerful tool, users may encounter certain issues during implementation. Below are some common problems and their solutions:
1. Connection Refused
Solution: Verify that the SSH server is running and that the correct port is being used. Check firewall settings to ensure that incoming connections are allowed.
2. Authentication Failed
Solution: Double-check your username and password or public key configuration. Ensure that the SSH server is configured to accept the chosen authentication method.
3. Slow Connection Speeds
Solution: Optimize SSH settings by disabling unused features and enabling compression. Additionally, ensure that your network connection is stable and free of interference.
Security Tips for IoT Devices
Securing IoT devices goes beyond implementing SSH. Below are some additional tips to enhance the overall security of your IoT ecosystem:
- Change default passwords immediately after deployment.
- Regularly update firmware and software to patch vulnerabilities.
- Segment your network to isolate IoT devices from critical systems.
- Monitor device activity for suspicious behavior and take immediate action if necessary.
Real-World Examples of SSH in IoT
SSH has been successfully implemented in various real-world IoT applications. Below are a few examples:
1. Smart Home Automation
SSH is used to secure communication between smart home devices and central control systems, ensuring that sensitive data, such as security camera footage, remains protected.
2. Industrial IoT
In industrial settings, SSH secures communication between sensors, actuators, and control systems, safeguarding critical infrastructure from cyber threats.
3. Healthcare IoT
SSH plays a crucial role in securing medical devices, such as wearable health monitors and remote diagnostic tools, ensuring patient data privacy and compliance with regulations like HIPAA.
Conclusion
Securing IoT devices with SSH is a vital step in protecting your digital ecosystem from cyber threats. By following the guidelines outlined in this article, you can effectively implement SSH and enhance the security of your IoT devices. Remember to adhere to best practices, regularly update your software, and stay informed about the latest security trends.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insightful content on IoT security and related topics. Together, let's build a safer and more secure digital future!
Data Source: OpenSSH Official Website, PuTTY Official Website, Bitvise SSH Client.