In today's interconnected world, the Internet of Things (IoT) has revolutionized the way we interact with devices and data. IoT SSH server plays a pivotal role in securing and managing these connected systems. Whether you're a tech enthusiast, a developer, or a business owner, understanding the potential of IoT SSH server is crucial for leveraging its benefits effectively.
The concept of IoT SSH server might seem complex at first glance, but it essentially revolves around enabling secure communication between IoT devices and central servers. This secure communication is vital for maintaining privacy, protecting sensitive data, and ensuring the smooth operation of IoT networks.
As we delve deeper into this topic, you'll discover how IoT SSH server can enhance the security of your IoT ecosystem, streamline device management, and pave the way for innovative solutions. This comprehensive guide will provide you with the tools and knowledge needed to unlock the full potential of IoT SSH server technology.
Read also:Hdhub4ucom Your Ultimate Destination For Highquality Movies And Entertainment
Table of Contents
- Introduction to IoT SSH Server
- The Benefits of IoT SSH Server
- How IoT SSH Server Works
- Choosing the Right IoT SSH Server Solution
- Security Considerations for IoT SSH Server
- Common Use Cases for IoT SSH Server
- Best Practices for Implementing IoT SSH Server
- Tools and Software for IoT SSH Server
- Future Trends in IoT SSH Server Technology
- Conclusion and Next Steps
Introduction to IoT SSH Server
IoT SSH server stands as a cornerstone in the realm of secure communication for interconnected devices. Secure Shell (SSH) protocol has long been the standard for encrypted communication, and when applied to IoT, it ensures that data transmitted between devices remains secure and tamper-proof.
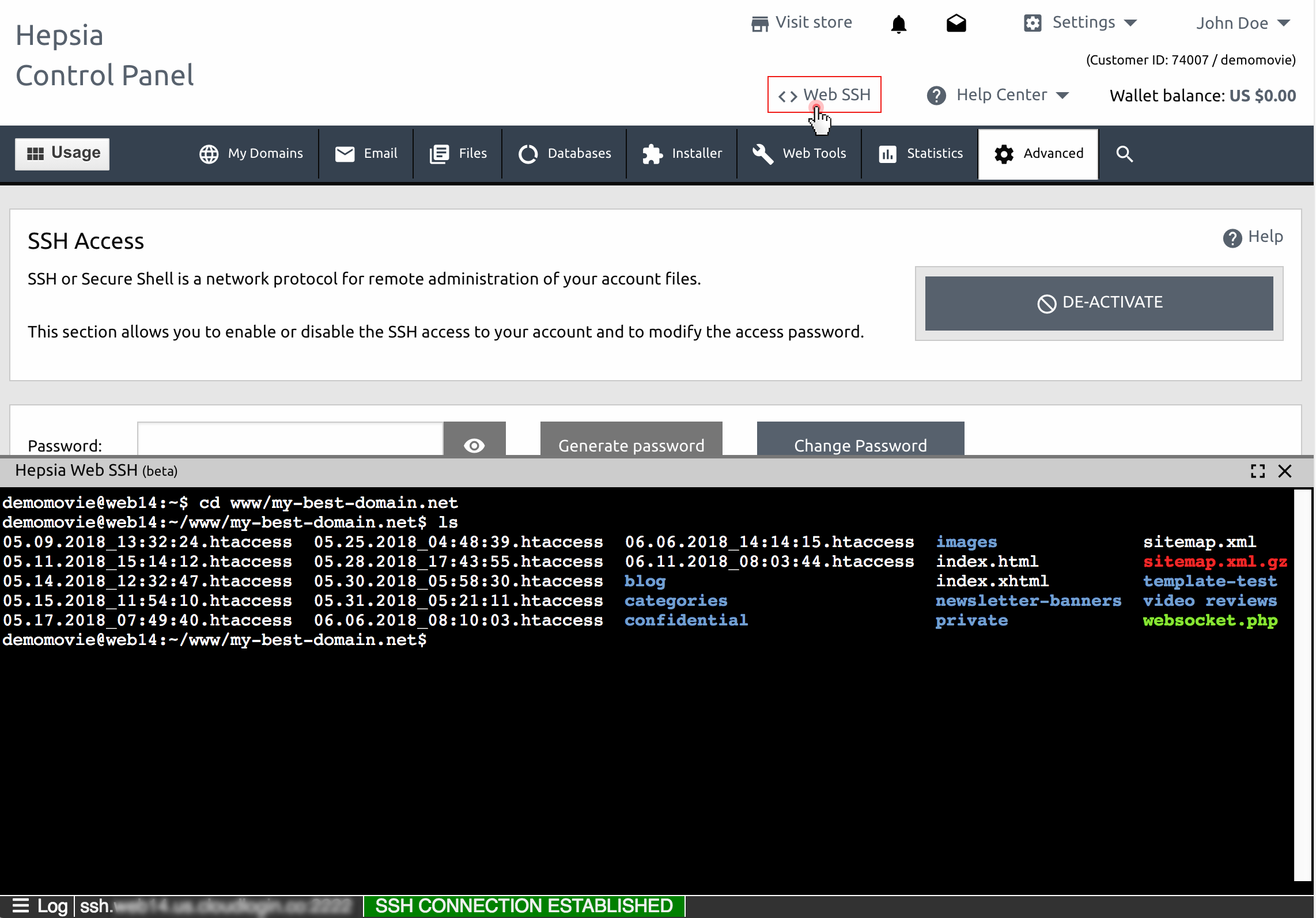
With the proliferation of IoT devices, the need for robust security measures has never been more critical. IoT SSH server addresses this need by providing a secure channel for device management, data transfer, and remote access. This section will explore the basics of IoT SSH server and its significance in modern IoT ecosystems.
What is an IoT SSH Server?
An IoT SSH server is a specialized application designed to facilitate secure communication between IoT devices and central servers using the SSH protocol. It acts as a gateway, enabling encrypted data exchange and ensuring that unauthorized access is prevented.
Why Use IoT SSH Server?
Using an IoT SSH server offers numerous advantages, including enhanced security, streamlined device management, and reliable data transfer. By implementing IoT SSH server solutions, organizations can safeguard their IoT networks from potential threats and vulnerabilities.
The Benefits of IoT SSH Server
Understanding the benefits of IoT SSH server is essential for anyone looking to implement this technology. Below are some of the key advantages:
- Enhanced Security: IoT SSH server ensures that all communication between devices and servers is encrypted, minimizing the risk of data breaches.
- Remote Access: Administrators can remotely access and manage IoT devices securely, improving operational efficiency.
- Scalability: IoT SSH server solutions can be scaled to accommodate growing IoT networks, ensuring flexibility and adaptability.
- Reliability: With robust encryption and authentication mechanisms, IoT SSH server ensures reliable and secure data transfer.
How IoT SSH Server Works
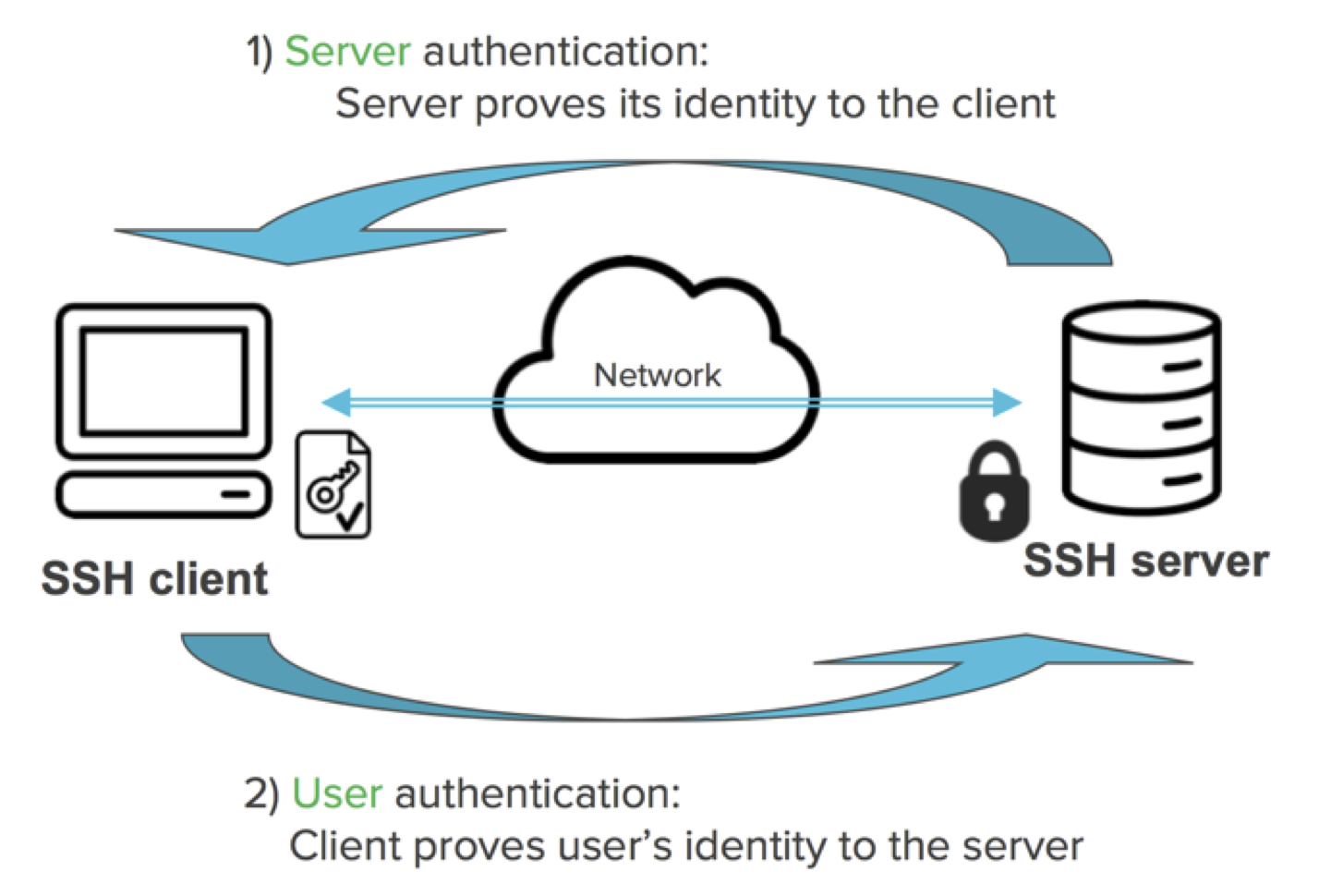
The functioning of an IoT SSH server involves several key components and processes. At its core, the server uses the SSH protocol to establish secure connections between devices and central servers. This section will break down the mechanics of IoT SSH server operation.
Read also:Discovering Mkvmoviespoint Your Gateway To Cinematic Treasures
Key Components of IoT SSH Server
- SSH Protocol: The foundation of IoT SSH server, providing encryption and authentication for secure communication.
- Client-Server Architecture: IoT devices act as clients, connecting to the central server through the IoT SSH server.
- Encryption Algorithms: Advanced encryption methods ensure that data remains secure during transmission.
Step-by-Step Process
The process begins with the IoT device initiating a connection to the central server via the IoT SSH server. The server authenticates the device and establishes an encrypted channel for data transfer. This ensures that all communication remains secure and protected from unauthorized access.
Choosing the Right IoT SSH Server Solution
Selecting the appropriate IoT SSH server solution is crucial for maximizing its benefits. Factors such as scalability, compatibility, and ease of use should be considered when making this decision. Below are some tips for choosing the right IoT SSH server solution:
- Assess your organization's specific needs and requirements.
- Consider the scalability of the solution to accommodate future growth.
- Evaluate the compatibility of the solution with existing systems and devices.
Security Considerations for IoT SSH Server
While IoT SSH server enhances security, it's important to address potential vulnerabilities and risks. This section will highlight key security considerations for IoT SSH server implementation.
Common Security Threats
- Brute Force Attacks: Unauthorized attempts to gain access by repeatedly guessing passwords.
- Man-in-the-Middle Attacks: Interception of communication between devices and servers.
- Configuration Errors: Improper setup leading to security loopholes.
Best Security Practices
To mitigate these threats, it's essential to follow best security practices such as using strong passwords, enabling two-factor authentication, and regularly updating software and firmware.
Common Use Cases for IoT SSH Server
IoT SSH server finds applications in various industries and scenarios. Below are some common use cases:
- Smart Home Automation: Securing communication between smart home devices and central hubs.
- Industrial IoT: Managing and monitoring industrial devices and machinery remotely.
- Healthcare: Ensuring secure data transfer for medical devices and systems.
Best Practices for Implementing IoT SSH Server
Implementing IoT SSH server requires careful planning and execution. Below are some best practices to ensure successful implementation:
- Conduct thorough research and testing before deployment.
- Train personnel on the proper use and maintenance of IoT SSH server.
- Regularly monitor and audit the system for potential security issues.
Tools and Software for IoT SSH Server
Various tools and software are available to facilitate the implementation and management of IoT SSH server. Some popular options include OpenSSH, PuTTY, and Bitvise SSH Client. These tools offer features such as secure file transfer, remote command execution, and session management.
Future Trends in IoT SSH Server Technology
The future of IoT SSH server technology holds exciting possibilities. Emerging trends such as quantum-safe encryption, blockchain integration, and AI-driven security are expected to shape the evolution of IoT SSH server solutions. Staying informed about these trends will help organizations prepare for the future of IoT security.
Conclusion and Next Steps
In conclusion, unlocking the power of IoT SSH server offers immense potential for securing and managing IoT ecosystems. By understanding its benefits, functioning, and implementation best practices, organizations can harness its capabilities to drive innovation and efficiency.
We encourage you to take the next step by exploring the tools and software mentioned in this guide and implementing IoT SSH server solutions in your projects. Share your thoughts and experiences in the comments below, and don't forget to check out our other articles for more insights into IoT and related technologies.
Sources: