As the Internet of Things (IoT) continues to evolve, remote login capabilities for IoT devices on AWS have become indispensable for businesses and developers alike. The ability to securely access and manage IoT devices remotely is critical for maintaining operational efficiency and ensuring data integrity. In this comprehensive guide, we will explore how to master remote login for IoT devices on AWS, providing you with the tools and knowledge necessary to implement secure and scalable solutions.
With the rise of connected devices, IoT applications are expanding rapidly across industries. From smart homes to industrial automation, IoT devices are transforming the way we interact with technology. However, managing these devices remotely poses unique challenges, particularly when it comes to security and scalability. This guide will address these challenges head-on, offering practical insights and best practices.
By the end of this article, you will have a clear understanding of the key concepts, tools, and strategies required to master remote login for IoT devices on AWS. Whether you are a developer, IT professional, or business leader, this guide will equip you with the expertise needed to navigate this complex yet rewarding field.
Read also:Haiden Deegan Dad A Comprehensive Look Into The Life And Legacy Of A Motocross Legend
Table of Contents
- Introduction to Remote Login for IoT Devices
- AWS IoT Core Overview
- Security Best Practices for Remote Login
- Scalability and Performance Considerations
- Authentication Methods for IoT Devices
- Remote Management of IoT Devices
- Data Encryption for Secure Communication
- Monitoring and Logging for IoT Devices
- Troubleshooting Common Issues
- Future Trends in IoT Remote Login
- Conclusion
Introduction to Remote Login for IoT Devices
Remote login for IoT devices on AWS is a critical capability that enables users to access and manage devices from anywhere in the world. This functionality is particularly important for organizations that rely on IoT solutions to monitor and control critical infrastructure. AWS provides a robust platform for implementing secure and scalable remote login solutions, leveraging its extensive suite of services.
Understanding the fundamentals of remote login is essential for anyone working with IoT devices. This section will cover the basic concepts, including the role of AWS IoT Core, the importance of secure communication protocols, and the benefits of remote management. By mastering these fundamentals, you will be better equipped to design and implement effective remote login solutions.
Additionally, we will explore the challenges associated with remote login, such as security vulnerabilities and network limitations. Addressing these challenges requires a comprehensive approach that incorporates best practices and cutting-edge technologies. This guide will provide you with the insights needed to overcome these obstacles and achieve success in your IoT projects.
AWS IoT Core Overview
Understanding AWS IoT Core
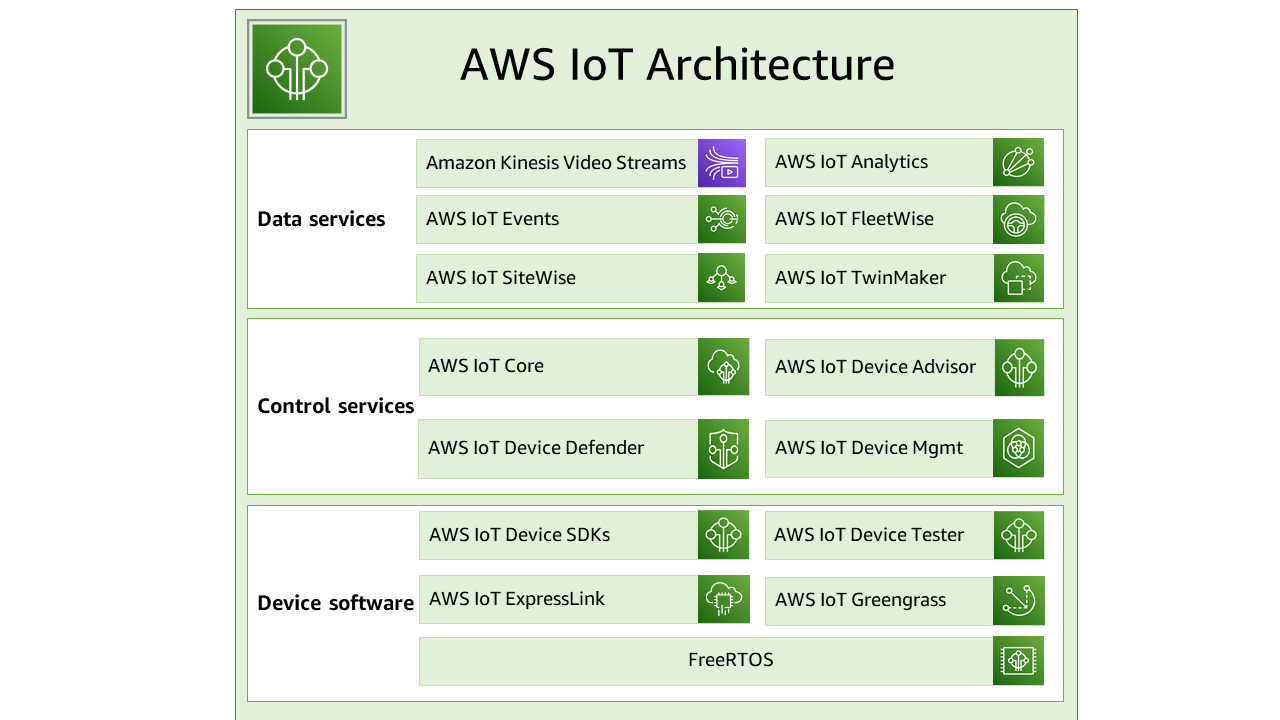
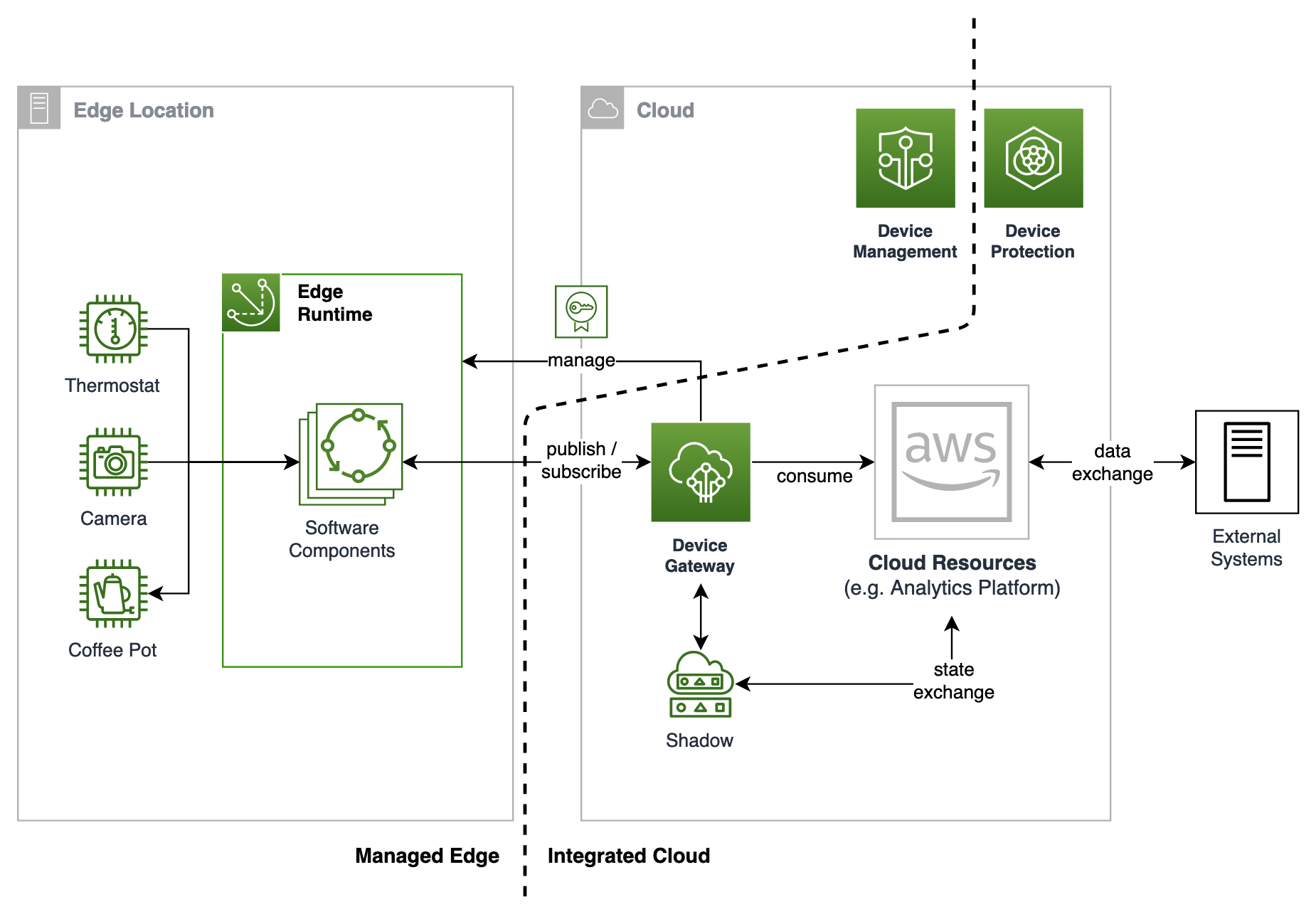
AWS IoT Core is a managed cloud service that allows connected devices to securely interact with cloud applications and other devices. It serves as the backbone of AWS's IoT ecosystem, providing essential features such as device registration, message routing, and data processing. For remote login, AWS IoT Core plays a pivotal role in facilitating secure and reliable communication between devices and users.
Key features of AWS IoT Core include:
- Device Shadow: Allows users to manage device states even when the device is offline.
- MQTT and HTTP Protocols: Supports multiple communication protocols for flexible integration.
- Rules Engine: Enables automated processing of device data using SQL-based rules.
By leveraging AWS IoT Core, developers can build scalable and secure remote login solutions that meet the demands of modern IoT applications.
Read also:1tamilblasters New Link 2025 Your Ultimate Guide To Accessing Tamil Movies
Security Best Practices for Remote Login
Ensuring Secure Communication
Security is paramount when it comes to remote login for IoT devices. Without proper safeguards, sensitive data and critical infrastructure could be exposed to malicious actors. To mitigate these risks, it is essential to implement security best practices that address both device and network vulnerabilities.
Some key security measures include:
- Using strong authentication mechanisms, such as certificates and tokens.
- Encrypting all data transmissions using protocols like TLS.
- Implementing role-based access control (RBAC) to restrict user permissions.
In addition to these measures, regular security audits and vulnerability assessments are crucial for maintaining a secure environment. By adhering to these best practices, you can significantly reduce the risk of security breaches and ensure the integrity of your IoT systems.
Scalability and Performance Considerations
Building Scalable Solutions
As IoT deployments grow in size and complexity, scalability becomes a critical consideration for remote login solutions. AWS offers a range of services and tools that enable developers to build scalable and high-performance systems capable of handling large volumes of data and devices.
To ensure scalability, consider the following strategies:
- Utilize AWS Lambda for serverless computing to process device data efficiently.
- Implement caching mechanisms to reduce latency and improve response times.
- Monitor system performance using AWS CloudWatch to identify and address bottlenecks.
By designing your remote login solution with scalability in mind, you can ensure that it remains effective as your IoT deployment grows and evolves.
Authentication Methods for IoT Devices
Choosing the Right Authentication Mechanism
Authentication is a critical component of secure remote login for IoT devices. Selecting the appropriate authentication method depends on factors such as device capabilities, network constraints, and security requirements. AWS provides several authentication options, each with its own strengths and limitations.
Common authentication methods include:
- Certificate-based authentication: Ideal for devices with secure storage capabilities.
- Token-based authentication: Suitable for resource-constrained devices.
- Username and password: Simple but less secure compared to other methods.
Understanding the trade-offs between these methods will help you choose the best option for your specific use case. Additionally, combining multiple authentication mechanisms can provide an additional layer of security for your IoT devices.
Remote Management of IoT Devices
Streamlining Device Management
Remote management is a key aspect of IoT device administration, enabling users to perform tasks such as firmware updates, configuration changes, and troubleshooting without physical access to the device. AWS offers several tools and services that simplify remote management, including AWS IoT Device Management and AWS Systems Manager.
Key features of remote management tools include:
- Device provisioning and registration.
- Over-the-air (OTA) updates for firmware and software.
- Remote diagnostics and troubleshooting capabilities.
By leveraging these tools, you can streamline the management of your IoT devices and improve overall operational efficiency.
Data Encryption for Secure Communication
Protecting Data in Transit and at Rest
Data encryption is a fundamental security measure for remote login solutions, ensuring that sensitive information remains confidential both during transmission and while stored. AWS provides robust encryption capabilities that can be integrated into your IoT applications to enhance security.
Some encryption options include:
- Transport Layer Security (TLS): Encrypts data in transit between devices and the cloud.
- AWS Key Management Service (KMS): Manages encryption keys for data at rest.
- Client-side encryption: Encrypts data before it is sent to the cloud for added protection.
Implementing encryption is a critical step in securing your IoT systems and protecting against data breaches.
Monitoring and Logging for IoT Devices
Enhancing System Visibility
Monitoring and logging are essential for maintaining the health and security of IoT systems. By collecting and analyzing device data, you can gain valuable insights into system performance, identify potential issues, and respond to incidents in real time. AWS provides several tools for monitoring and logging, including AWS CloudWatch and AWS IoT Analytics.
Key benefits of monitoring and logging include:
- Real-time visibility into device activity and performance metrics.
- Automated alerts for abnormal behavior or security threats.
- Comprehensive logs for auditing and compliance purposes.
By implementing effective monitoring and logging strategies, you can enhance the reliability and security of your IoT systems.
Troubleshooting Common Issues
Addressing Challenges in Remote Login
Despite careful planning and implementation, challenges may arise when managing remote login for IoT devices. Common issues include connectivity problems, authentication failures, and performance bottlenecks. To address these challenges, it is important to have a solid troubleshooting strategy in place.
Some troubleshooting tips include:
- Check network connectivity and ensure proper device configuration.
- Verify authentication credentials and ensure they are up to date.
- Analyze logs and performance metrics to identify and resolve issues.
By following these tips, you can quickly diagnose and resolve issues, minimizing downtime and ensuring the smooth operation of your IoT systems.
Future Trends in IoT Remote Login
Exploring Emerging Technologies
The field of IoT remote login is rapidly evolving, driven by advancements in technology and changing user requirements. Emerging trends such as edge computing, artificial intelligence, and quantum cryptography are shaping the future of IoT security and management. Staying informed about these trends is essential for remaining competitive and innovative in the IoT space.
Key trends to watch include:
- Edge computing: Reduces latency and improves performance by processing data closer to the source.
- Artificial intelligence: Enhances security and automation through machine learning algorithms.
- Quantum cryptography: Provides advanced encryption techniques for ultra-secure communication.
By embracing these trends, you can position yourself at the forefront of IoT innovation and take full advantage of the opportunities they present.
Conclusion
In conclusion, mastering remote login for IoT devices on AWS requires a comprehensive understanding of the tools, technologies, and best practices involved. By leveraging AWS's robust platform and following the guidance provided in this article, you can build secure, scalable, and efficient remote login solutions that meet the needs of your IoT applications.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and cloud computing. Together, we can continue to advance the field of IoT and unlock its full potential for businesses and individuals alike.