In the era of interconnected devices, mastering IoT remote access through SSH free methods has become a crucial skill for tech enthusiasts and professionals alike. As the Internet of Things (IoT) continues to expand, understanding how to remotely manage and secure devices is essential for optimizing performance and maintaining security. Whether you're a beginner or an advanced user, this guide will walk you through everything you need to know about IoT remote access via SSH without any cost barriers.
With IoT devices increasingly becoming part of our daily lives, remote access is no longer a luxury but a necessity. From smart homes to industrial automation, the ability to access and control devices remotely ensures seamless operation and troubleshooting. In this ultimate guide, we'll explore the foundations of SSH, its role in IoT, and how you can implement it for free while ensuring maximum security.
Whether you're looking to enhance your skills, improve your IoT setup, or simply stay updated with the latest trends, this article is designed to provide comprehensive insights. By the end of this guide, you'll have the tools and knowledge to confidently deploy SSH-based remote access solutions for your IoT devices.
Read also:Mothers Warmth Jackerman Chapter 3 A Deep Dive Into The Story And Its Meaning
Table of Contents
- What is SSH and Why Is It Important for IoT?
- The Role of SSH in IoT Remote Access
- Setting Up SSH for IoT Devices
- Free SSH Options for IoT Enthusiasts
- Security Best Practices for IoT SSH Access
- Troubleshooting Common SSH Issues
- Alternatives to SSH for IoT Remote Access
- Real-World Use Cases of IoT SSH Remote Access
- Future Trends in IoT Remote Access
- Conclusion: Take Your IoT Skills to the Next Level
What is SSH and Why Is It Important for IoT?
SSH, or Secure Shell, is a cryptographic protocol used for secure communication between devices over an unsecured network. It provides a safe and encrypted way to access remote servers, making it ideal for IoT applications where security is paramount. Unlike traditional methods, SSH ensures that data transmitted between devices remains private and tamper-proof.
In the context of IoT, SSH plays a critical role in enabling remote management of devices. Whether you're configuring sensors, updating firmware, or troubleshooting connectivity issues, SSH offers a reliable and secure solution. By mastering SSH, you can streamline your IoT operations while minimizing security risks.
Key benefits of using SSH for IoT include:
- Encrypted communication for enhanced security
- Remote command execution for efficient device management
- Support for file transfers using SFTP
The Role of SSH in IoT Remote Access
Understanding IoT Remote Access
Remote access in IoT refers to the ability to interact with and control devices from a distance. This functionality is vital for maintaining and monitoring IoT setups, especially in scenarios where physical access is limited or impractical. SSH serves as a cornerstone for secure remote access, providing a robust framework for interacting with IoT devices.
How SSH Enhances IoT Security
One of the primary challenges in IoT is ensuring the security of data transmitted between devices. SSH addresses this concern by encrypting all communication, making it virtually impossible for unauthorized parties to intercept or manipulate data. Additionally, SSH supports authentication mechanisms such as public-key cryptography, which adds an extra layer of security.
By leveraging SSH for IoT remote access, you can:
Read also:Latest Craze Viral Indian Mms Videos Exposeacute A Comprehensive Analysis
- Securely connect to devices over public networks
- Automate routine tasks using scripts and commands
- Monitor device performance in real-time
Setting Up SSH for IoT Devices
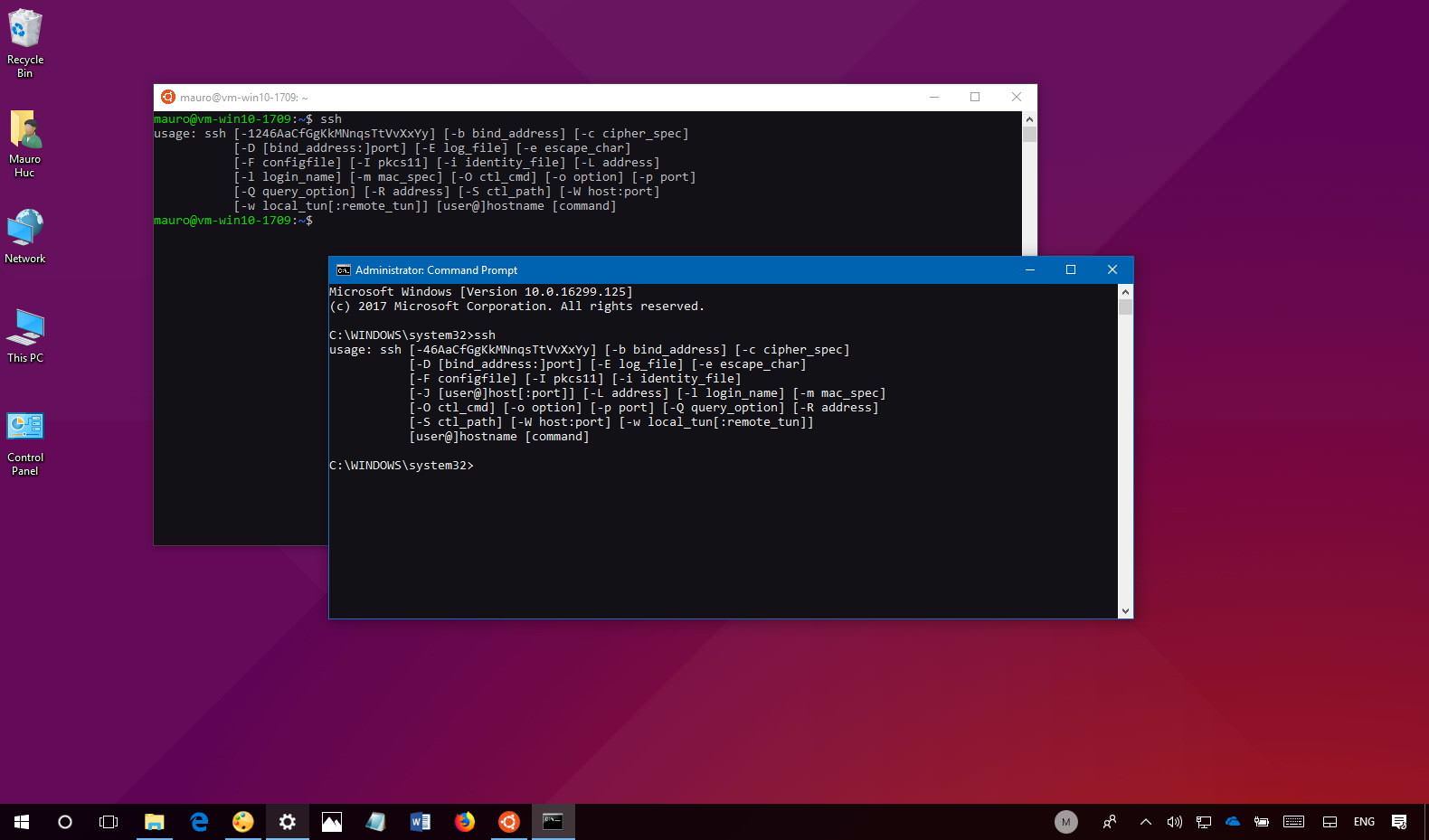
Step-by-Step Guide to Configuring SSH
Setting up SSH on an IoT device involves a few straightforward steps. Below is a comprehensive guide to help you get started:
- Install SSH Server: Ensure that your IoT device has an SSH server installed. Most Linux-based systems, such as Raspberry Pi, come with OpenSSH pre-installed.
- Enable SSH Service: Use the device's configuration tools to enable the SSH service. For example, on a Raspberry Pi, you can enable SSH through the Raspberry Pi Configuration utility.
- Configure Firewall Rules: Adjust your firewall settings to allow incoming SSH connections on port 22 (or a custom port if you prefer).
- Test the Connection: Use an SSH client on your local machine to connect to the IoT device and verify that the setup is functioning correctly.
Tips for Streamlining SSH Setup
To make the SSH setup process smoother, consider the following tips:
- Use strong passwords or public-key authentication for enhanced security
- Regularly update your SSH server to protect against vulnerabilities
- Document your configuration steps for future reference
Free SSH Options for IoT Enthusiasts
OpenSSH: The Go-To Solution
OpenSSH is one of the most widely used SSH implementations and is available for free on virtually all Linux-based systems. Its open-source nature ensures that it is regularly updated and maintained by a vibrant community of developers. Additionally, OpenSSH offers a wide range of features, including support for public-key authentication, tunneling, and port forwarding.
Alternative Free Tools
Besides OpenSSH, several other free tools can facilitate IoT remote access via SSH:
- Bitvise SSH Client: A user-friendly SSH client for Windows that offers advanced features such as SFTP and terminal emulation.
- Putty: A lightweight and free SSH client that is perfect for beginners and advanced users alike.
- Mosh (Mobile Shell): An SSH alternative designed for unstable network connections, ensuring seamless access even in challenging environments.
Security Best Practices for IoT SSH Access
Securing Your SSH Configuration
While SSH provides a secure foundation for IoT remote access, it is essential to implement additional security measures to protect your devices. Below are some best practices to consider:
- Change Default Port: Modify the default SSH port (22) to a non-standard port to reduce the risk of automated attacks.
- Disable Password Authentication: Use public-key authentication instead of relying on passwords to enhance security.
- Limit User Access: Restrict SSH access to specific users or IP addresses to minimize the attack surface.
Monitoring and Logging SSH Activity
Regularly monitoring SSH activity can help identify potential security threats and unauthorized access attempts. Enable logging on your SSH server and review logs periodically to ensure the integrity of your IoT setup.
Troubleshooting Common SSH Issues
Connection Errors
If you encounter connection issues while trying to access your IoT device via SSH, consider the following troubleshooting steps:
- Verify that the SSH service is running on the device
- Check your network configuration and ensure that the device is reachable
- Review firewall rules to ensure that SSH traffic is allowed
Authentication Problems
Authentication-related issues can arise due to incorrect credentials or misconfigured settings. To resolve these problems:
- Double-check your username and password
- Ensure that public-key authentication is properly set up
- Consult the SSH server logs for detailed error messages
Alternatives to SSH for IoT Remote Access
VNC: Visual Remote Access
While SSH is ideal for command-line interactions, VNC (Virtual Network Computing) offers a graphical interface for remote access. This can be particularly useful for IoT devices with graphical user interfaces, such as smart displays or kiosks.
MQTT: Lightweight Messaging Protocol
For scenarios where real-time data exchange is critical, MQTT (Message Queuing Telemetry Transport) provides a lightweight alternative to SSH. MQTT is widely used in IoT applications for its low bandwidth requirements and efficient communication.
Real-World Use Cases of IoT SSH Remote Access
Smart Home Automation
SSH enables homeowners to remotely manage their smart home devices, such as lighting systems, thermostats, and security cameras. By leveraging SSH, users can ensure that their devices remain secure and functional at all times.
Industrial IoT Monitoring
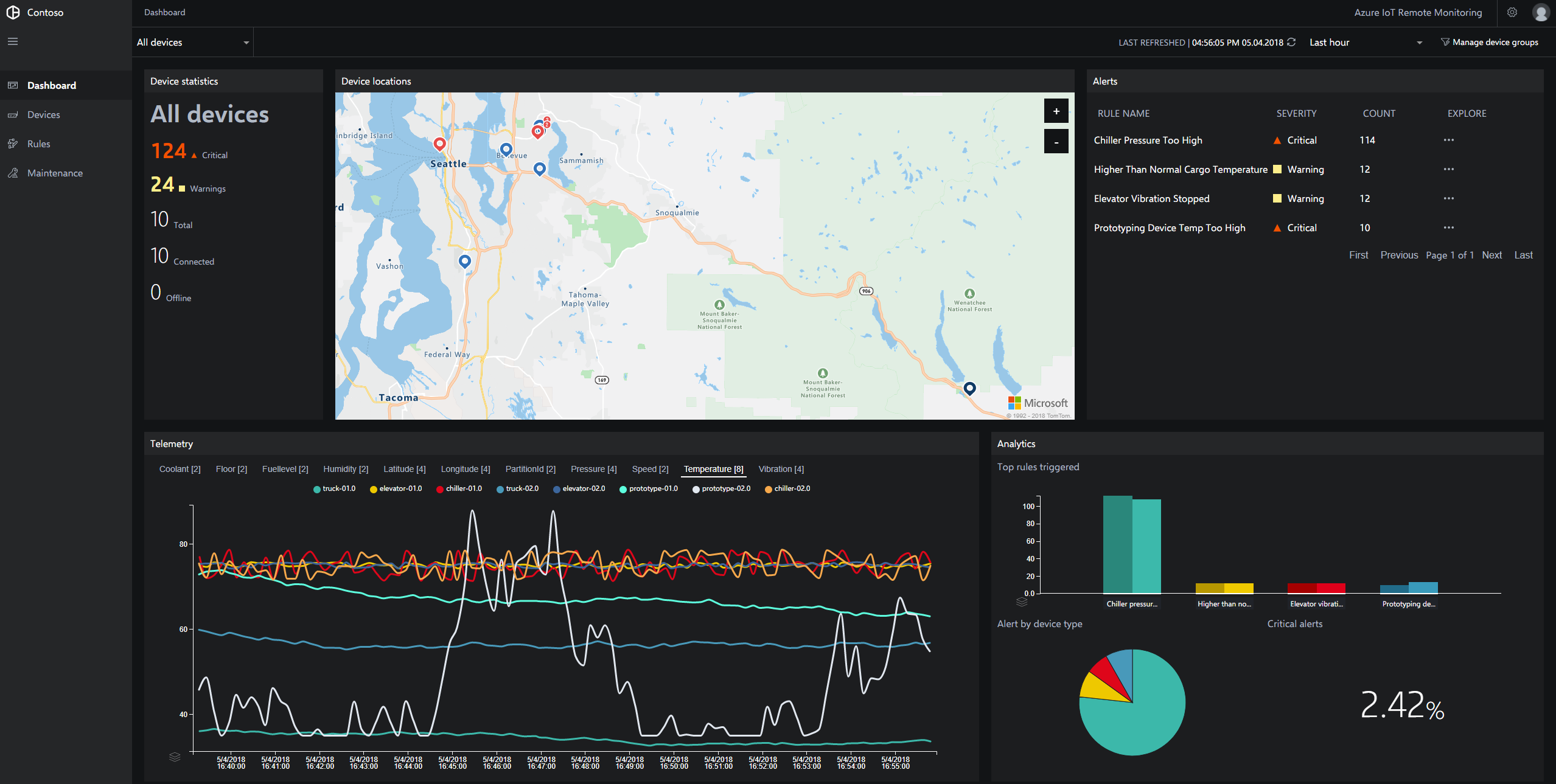
In industrial settings, SSH plays a vital role in monitoring and controlling IoT devices used for manufacturing, logistics, and asset management. Remote access capabilities allow engineers to troubleshoot issues and optimize operations without needing to be physically present.
Future Trends in IoT Remote Access
Quantum-Safe Encryption
As quantum computing becomes more prevalent, the need for quantum-safe encryption methods will grow. Future SSH implementations may incorporate post-quantum cryptographic algorithms to ensure long-term security for IoT devices.
Edge Computing Integration
With the rise of edge computing, IoT remote access solutions will increasingly focus on decentralizing data processing and storage. This trend will lead to more efficient and scalable SSH implementations tailored for edge devices.
Conclusion: Take Your IoT Skills to the Next Level
In conclusion, mastering IoT remote access via SSH is an invaluable skill for anyone involved in the IoT ecosystem. By understanding the principles of SSH and implementing best practices, you can ensure secure and efficient management of your IoT devices. This ultimate guide has provided you with the knowledge and tools to confidently deploy SSH-based solutions for your IoT projects.
We encourage you to take action by experimenting with SSH on your own IoT devices. Share your experiences in the comments below and explore other articles on our site to further enhance your IoT expertise. Together, let's shape the future of interconnected technology!