Accessing your Raspberry Pi from the internet can provide immense convenience for remote management and monitoring. However, it also comes with significant security risks that must be addressed. Securing your Raspberry Pi is crucial to protect it from unauthorized access and potential cyberattacks.
In this digital era, remote access to devices like Raspberry Pi has become increasingly popular. Whether you're using it as a media server, a home automation hub, or a web server, being able to connect to it from anywhere in the world is highly desirable. However, the question remains: how can you safely access Raspberry Pi from the internet without compromising its security?
This article will guide you through the steps to securely access your Raspberry Pi from the internet, ensuring your device remains protected while still offering the flexibility of remote connectivity. By following best practices, you can enjoy the benefits of remote access without exposing your system to unnecessary risks.
Read also:Taecyeon Wife A Complete Guide To The Life And Love Of The Kpop Star
Table of Contents
- Introduction
- Understanding Raspberry Pi
- Why Secure Remote Access Matters
- Step-by-Step Setup for Remote Access
- Secure SSH Connection
- Use a VPN for Enhanced Security
- Additional Security Measures
- Troubleshooting Common Issues
- Best Practices for Safe Remote Access
- Conclusion
Introduction
The Raspberry Pi is a versatile, low-cost computer that has found its way into countless projects, from home automation to web hosting. One of the most sought-after features of the Raspberry Pi is the ability to access it remotely from the internet. However, this convenience must be balanced with robust security measures to prevent unauthorized access.
Learning how to safely access Raspberry Pi from the internet is essential for anyone who wants to leverage its full potential without compromising security. This article will explore the necessary steps and best practices to achieve this goal.
Whether you're a beginner or an experienced user, understanding the security implications of remote access is crucial. By following the guidelines provided here, you can ensure that your Raspberry Pi remains secure while still being accessible from anywhere in the world.
Understanding Raspberry Pi
The Raspberry Pi is a single-board computer designed for educational purposes, but it has evolved into a powerful tool for hobbyists and professionals alike. Its affordability and flexibility make it an ideal choice for a wide range of applications, including remote server management, media streaming, and IoT projects.
Before diving into the process of accessing your Raspberry Pi from the internet, it's important to understand its basic functionality and capabilities. The Raspberry Pi operates on a Linux-based operating system, such as Raspbian, which provides a robust platform for running various applications.
Some of the key features of the Raspberry Pi include:
Read also:Andie Elle A Deep Dive Into Her Life And The Buzz Around Andie Elle Nudes
- Compact size and low power consumption
- Support for multiple programming languages
- Compatibility with a wide range of peripherals
- Ability to run as a headless server
Why Secure Remote Access Matters
Remote access to your Raspberry Pi offers numerous benefits, but it also introduces potential security risks. Without proper security measures, your device could become vulnerable to cyberattacks, unauthorized access, and data breaches.
Some of the risks associated with remote access include:
- Brute-force attacks on SSH
- Malware infections
- Data theft
- Unintended exposure of sensitive information
By implementing secure remote access practices, you can mitigate these risks and ensure that your Raspberry Pi remains protected. This is particularly important if your device is hosting sensitive data or running critical applications.
Step-by-Step Setup for Remote Access
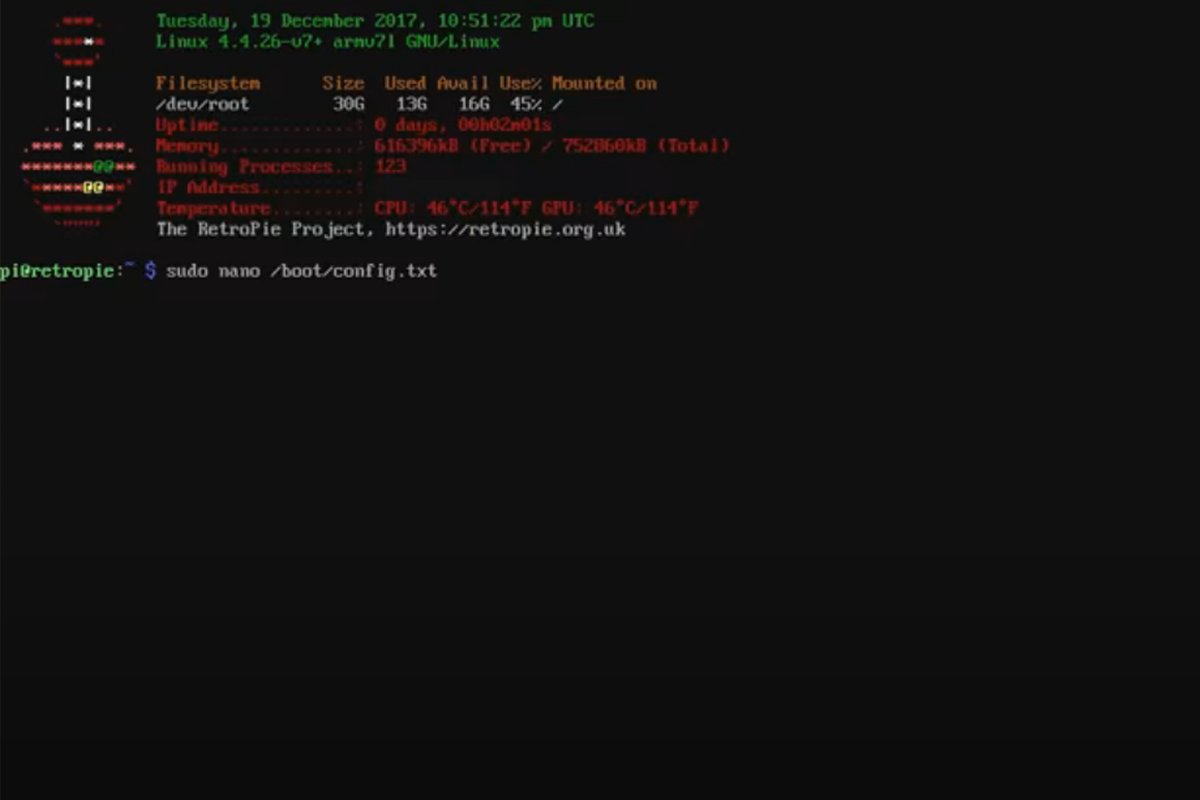
Install and Configure SSH
SSH (Secure Shell) is the most common method for remotely accessing a Raspberry Pi. To enable SSH on your Raspberry Pi, follow these steps:
- Ensure your Raspberry Pi is running the latest version of the operating system.
- Open the terminal and type
sudo raspi-config. - Navigate to "Interfacing Options" and select "SSH".
- Choose "Yes" to enable SSH and then reboot your Raspberry Pi.
Once SSH is enabled, you can connect to your Raspberry Pi using an SSH client like PuTTY (for Windows) or the terminal (for macOS/Linux).
Use Port Forwarding
Port forwarding allows you to map a port on your router to a specific device on your local network, such as your Raspberry Pi. This enables external devices to connect to your Raspberry Pi via the internet.
To set up port forwarding:
- Log in to your router's admin interface.
- Locate the port forwarding settings.
- Add a new rule that maps port 22 (the default SSH port) to the local IP address of your Raspberry Pi.
- Save the changes and test the connection.
It's important to note that exposing port 22 directly to the internet can increase the risk of brute-force attacks. To enhance security, consider changing the default SSH port to a non-standard port number.
Secure SSH Connection
Securing your SSH connection is crucial for protecting your Raspberry Pi from unauthorized access. Here are some best practices to enhance SSH security:
- Change the default SSH port: Use a non-standard port number to reduce the likelihood of automated attacks.
- Disable root login: Restrict root access to prevent attackers from gaining administrative privileges.
- Use strong passwords: Choose complex passwords that are difficult to guess or crack.
- Enable two-factor authentication (2FA): Add an extra layer of security by requiring a second form of verification.
By implementing these measures, you can significantly improve the security of your SSH connection and reduce the risk of unauthorized access.
Use a VPN for Enhanced Security
A Virtual Private Network (VPN) provides an encrypted tunnel between your device and the Raspberry Pi, ensuring that all communication remains secure and private. Using a VPN is one of the most effective ways to safely access Raspberry Pi from the internet.
To set up a VPN for your Raspberry Pi:
- Choose a reputable VPN provider that supports server hosting.
- Install the necessary software on your Raspberry Pi.
- Configure the VPN client to connect to the provider's server.
- Test the connection to ensure it's working correctly.
With a VPN in place, you can access your Raspberry Pi securely from anywhere in the world, even on public Wi-Fi networks.
Additional Security Measures
In addition to securing SSH and using a VPN, there are several other steps you can take to enhance the security of your Raspberry Pi:
- Keep software up to date: Regularly update your operating system and installed applications to patch known vulnerabilities.
- Use a firewall: Configure a firewall to restrict incoming and outgoing traffic to only necessary ports and IP addresses.
- Monitor logs: Regularly review system logs for any suspicious activity.
- Limit user access: Create separate user accounts with limited privileges for different users.
By combining these security measures, you can create a robust defense against potential threats.
Troubleshooting Common Issues
Even with proper setup, you may encounter issues when trying to access your Raspberry Pi from the internet. Here are some common problems and their solutions:
- Unable to connect via SSH: Check your router's port forwarding settings and ensure the Raspberry Pi's IP address is correct.
- Slow connection speed: Optimize your network configuration and consider upgrading your internet plan if necessary.
- VPN connection fails: Verify your VPN settings and ensure the provider's servers are operational.
If you're still experiencing issues, consult the official Raspberry Pi documentation or seek help from online forums and communities.
Best Practices for Safe Remote Access
To ensure the safest possible remote access to your Raspberry Pi, follow these best practices:
- Regularly back up your data to prevent loss in case of a security breach.
- Limit the number of devices that can access your Raspberry Pi by using IP whitelisting.
- Monitor your system for any signs of unauthorized access and take immediate action if necessary.
- Stay informed about the latest security trends and threats affecting Linux-based systems.
By adhering to these best practices, you can maintain a secure and reliable remote access setup for your Raspberry Pi.
Conclusion
Accessing your Raspberry Pi from the internet can greatly enhance its functionality, but it requires careful consideration of security measures. By following the steps outlined in this article, you can safely access your Raspberry Pi while minimizing the risk of unauthorized access.
Remember to regularly update your system, use strong passwords, and implement additional security measures like firewalls and two-factor authentication. With these precautions in place, you can enjoy the convenience of remote access without compromising the security of your device.
We encourage you to leave a comment or share this article with others who may find it useful. If you have any questions or need further assistance, feel free to reach out to our community or explore other resources available online.
Source: Raspberry Pi Official Documentation