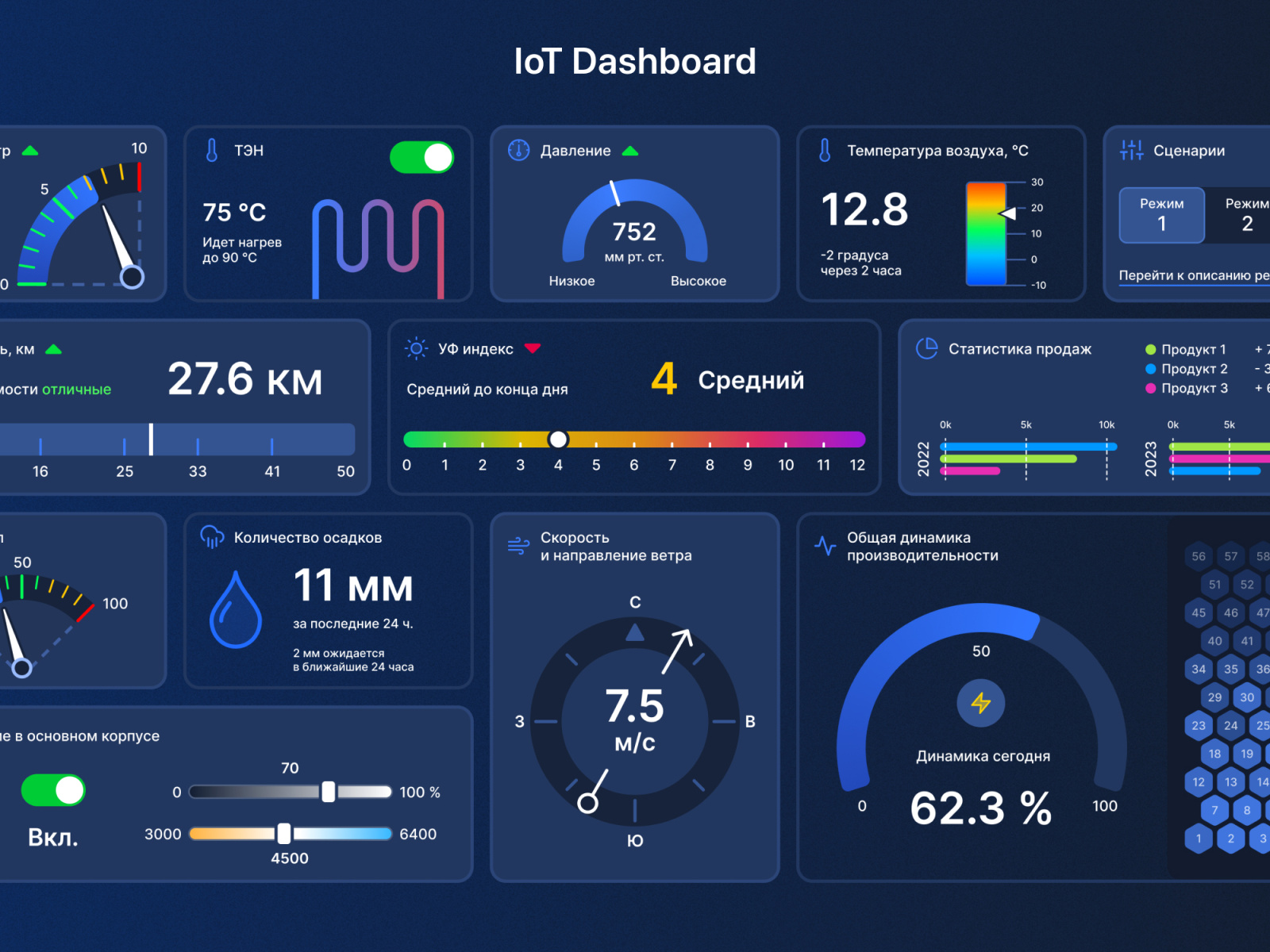
In today's digital age, the ability to access devices remotely has become a necessity for businesses and individuals alike. Best SSH IoT remotely free options offer secure and efficient ways to manage your devices without compromising on safety. Whether you're a tech enthusiast or a professional, understanding how remote access works can significantly enhance productivity and convenience.
Remote access through SSH (Secure Shell) protocols has become a cornerstone of modern networking. It allows users to control and manage IoT devices from anywhere in the world. With the growing demand for secure and cost-effective solutions, finding the best SSH IoT remotely free options is crucial. This article will guide you through the process, ensuring that you make an informed decision.
As technology continues to evolve, remote access tools have become more sophisticated. From enhanced security features to seamless connectivity, the best SSH IoT remotely free platforms provide users with the tools they need to stay connected. This article explores the top choices available, helping you unlock secure and efficient remote access for your devices.
Read also:Brandi Passante Nude Pics A Comprehensive Look At The Controversy And Its Impact
Understanding SSH and Its Role in IoT Remote Access
Secure Shell (SSH) is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. In the context of IoT (Internet of Things), SSH plays a critical role in ensuring that remote access is both secure and efficient. By encrypting data transmissions, SSH protects sensitive information from unauthorized access and potential cyber threats.
SSH is widely regarded as one of the most reliable protocols for remote access. Its ability to authenticate users and encrypt data makes it an ideal choice for IoT applications. Whether you're managing home automation systems, industrial sensors, or cloud-based services, SSH ensures that your devices remain secure and accessible from anywhere.
Key Features of SSH in IoT
- End-to-end encryption for secure data transmission.
- Strong user authentication mechanisms to prevent unauthorized access.
- Support for multiple devices and platforms, ensuring compatibility.
- Efficient resource utilization, minimizing bandwidth consumption.
By leveraging SSH, businesses and individuals can enjoy peace of mind knowing that their IoT devices are protected against potential threats. This section provides a foundational understanding of SSH and its importance in the realm of IoT remote access.
Benefits of Best SSH IoT Remotely Free Solutions
Choosing the best SSH IoT remotely free solutions offers numerous advantages. These platforms provide users with secure and efficient ways to manage their devices without incurring significant costs. Below are some of the key benefits:
1. Cost-Effectiveness
Free SSH IoT solutions eliminate the need for expensive proprietary software. This makes them an attractive option for small businesses and individuals looking to save on operational costs while maintaining high security standards.
2. Enhanced Security
With encryption and authentication features, the best SSH IoT remotely free platforms ensure that your devices are protected against unauthorized access and cyberattacks. This is particularly important in the IoT landscape, where devices are often vulnerable to security breaches.
Read also:When Does Serena And Dan Get Back Together In Season 2 A Deep Dive Into Their Iconic Relationship
3. Ease of Use
Many free SSH solutions come with user-friendly interfaces, making it easy for even novice users to set up and manage their remote access systems. This accessibility ensures that anyone can take advantage of these powerful tools without requiring extensive technical knowledge.
Top SSH IoT Remotely Free Platforms
When it comes to choosing the best SSH IoT remotely free platforms, there are several options available. Each platform offers unique features and capabilities, catering to different user needs. Below are some of the top choices:
1. OpenSSH
OpenSSH is one of the most widely used SSH implementations, providing robust security features and seamless integration with various operating systems. It supports multiple encryption algorithms and authentication methods, ensuring that your IoT devices remain secure.
2. PuTTY
PuTTY is a popular SSH client for Windows users, offering a simple and intuitive interface. It supports a wide range of protocols, including SSH, Telnet, and Rlogin, making it a versatile tool for remote access.
3. MobaXterm
MobaXterm is an advanced SSH client that combines the features of a terminal emulator, network tools, and an X11 server. Its all-in-one design makes it an ideal choice for users who require a comprehensive remote access solution.
How to Set Up SSH for IoT Remote Access
Setting up SSH for IoT remote access involves several steps. Below is a step-by-step guide to help you configure your devices:
Step 1: Install SSH Server
Begin by installing an SSH server on your IoT device. For Linux-based systems, you can use OpenSSH, which is available in most package repositories. Use the following command to install OpenSSH:
sudo apt-get install openssh-server
Step 2: Configure SSH Settings
Once the SSH server is installed, configure its settings to enhance security. Edit the SSH configuration file located at /etc/ssh/sshd_config. Modify parameters such as port number, authentication methods, and encryption algorithms to suit your needs.
Step 3: Test Remote Access
After configuring the SSH server, test the remote access functionality. Use an SSH client like PuTTY or MobaXterm to connect to your IoT device. Ensure that the connection is secure and that you can access all necessary features.
Security Best Practices for SSH IoT Remote Access
While SSH provides a secure method for remote access, it's essential to follow best practices to further enhance security. Below are some recommendations:
- Use strong passwords or public key authentication to prevent unauthorized access.
- Disable root login and create separate user accounts with limited privileges.
- Regularly update your SSH server and client software to protect against vulnerabilities.
- Monitor access logs to detect and respond to potential security threats.
By adhering to these guidelines, you can ensure that your IoT devices remain secure and protected against potential cyberattacks.
Common Challenges in SSH IoT Remote Access
Despite its advantages, SSH IoT remote access presents several challenges. These include:
1. Network Connectivity Issues
Poor network connectivity can hinder the effectiveness of SSH remote access. Ensure that your devices are connected to a stable and reliable network to avoid disruptions.
2. Compatibility Problems
Not all devices and platforms are compatible with SSH. Before implementing a remote access solution, verify that your devices support SSH and that they can integrate seamlessly with your chosen platform.
3. Security Threats
As with any networked system, SSH IoT remote access is susceptible to security threats. Regularly update your software and follow best practices to mitigate these risks.
Future Trends in SSH IoT Remote Access
The field of SSH IoT remote access continues to evolve, with new technologies and innovations emerging regularly. Some of the key trends to watch include:
1. Quantum-Resistant Encryption
As quantum computing becomes more prevalent, researchers are developing encryption algorithms that can withstand quantum-based attacks. These advancements will enhance the security of SSH IoT remote access systems.
2. AI-Driven Security
Artificial intelligence is being integrated into security systems to detect and respond to threats in real-time. This technology will play a crucial role in safeguarding SSH IoT remote access platforms against cyberattacks.
3. Cloud-Based Solutions
Cloud-based SSH solutions are becoming increasingly popular due to their scalability and ease of use. These platforms offer users the flexibility to manage their devices from anywhere, without the need for extensive infrastructure.
Conclusion
In conclusion, the best SSH IoT remotely free solutions provide secure and efficient ways to manage your devices from anywhere in the world. By understanding the key features, benefits, and challenges of these platforms, you can make an informed decision that meets your specific needs. Remember to follow security best practices and stay updated on the latest trends to ensure that your remote access system remains secure and effective.
We invite you to share your thoughts and experiences in the comments section below. Your feedback helps us improve and provides valuable insights for other readers. Additionally, feel free to explore our other articles for more information on SSH IoT remote access and related topics.
Table of Contents
- Understanding SSH and Its Role in IoT Remote Access
- Benefits of Best SSH IoT Remotely Free Solutions
- Top SSH IoT Remotely Free Platforms
- How to Set Up SSH for IoT Remote Access
- Security Best Practices for SSH IoT Remote Access
- Common Challenges in SSH IoT Remote Access
- Future Trends in SSH IoT Remote Access
- Key Features of SSH in IoT
- Cost-Effectiveness
- Ease of Use