As the Internet of Things (IoT) continues to grow, managing IoT devices behind a firewall has become a critical challenge for businesses and organizations. With billions of connected devices now in use, ensuring security, efficiency, and compliance is no longer optional. In this guide, we will delve into the best practices for managing IoT devices while maintaining robust security protocols.
The proliferation of IoT devices has transformed the way businesses operate, offering unprecedented opportunities for automation, data collection, and process optimization. However, this transformation also brings significant risks, particularly when it comes to cybersecurity. IoT devices, by their very nature, are often vulnerable to attacks if not properly managed behind a firewall.
This article is designed to provide a comprehensive roadmap for effectively managing IoT devices in a secure and efficient manner. Whether you're a network administrator, IT professional, or business owner, this guide will equip you with the knowledge and tools necessary to safeguard your IoT ecosystem.
Read also:Chad Michael Murrays Wife A Closer Look At Their Love Story And Life Together
Table of Contents
- Introduction to IoT Security
- Challenges of Managing IoT Behind a Firewall
- Understanding Firewalls and Their Role in IoT Security
- Best Practices for Managing IoT Devices Behind a Firewall
- The Importance of Network Segmentation
- Effective IoT Device Management
- Protecting Data in IoT Networks
- Continuous Monitoring and Threat Detection
- Regular Updates and Patch Management
- Future Trends in IoT Security
- Conclusion and Next Steps
Introduction to IoT Security
IoT devices have revolutionized industries by enabling real-time data collection and automation. However, with this innovation comes the need for robust security measures. Managing IoT devices effectively behind a firewall is crucial to protecting sensitive data and ensuring business continuity.
In this section, we explore the basics of IoT security and why firewalls play a pivotal role in safeguarding IoT ecosystems. Firewalls act as the first line of defense, filtering out malicious traffic and ensuring that only authorized devices can access the network.
By understanding the fundamentals of IoT security, organizations can take proactive steps to mitigate risks and protect their digital assets.
Challenges of Managing IoT Behind a Firewall
Device Diversity and Complexity
One of the primary challenges in managing IoT devices behind a firewall is the sheer diversity and complexity of these devices. IoT ecosystems often consist of devices from multiple vendors, each with its own set of protocols and security standards.
- Varied device types and operating systems
- Inconsistent security protocols
- Limited device resources for security features
Scalability Issues
As IoT networks grow, managing them becomes increasingly complex. Scalability is a significant challenge, particularly for organizations with large-scale IoT deployments. Ensuring that firewalls can handle the growing volume of traffic without compromising performance is essential.
Understanding Firewalls and Their Role in IoT Security
A firewall is a network security system that monitors and controls incoming and outgoing network traffic based on predetermined security rules. In the context of IoT, firewalls are critical for filtering traffic and preventing unauthorized access to IoT devices.
Read also:Unveiling The Scandal Indian Influencers Leaked Porn Ndash The Truth Behind The Headlines
Modern firewalls offer advanced features such as deep packet inspection, intrusion detection, and application control, making them indispensable for securing IoT networks. By understanding how firewalls function, organizations can better protect their IoT devices and data.
Best Practices for Managing IoT Devices Behind a Firewall
Implementing Strong Authentication
One of the most effective ways to secure IoT devices is by implementing strong authentication mechanisms. This includes using multi-factor authentication (MFA) and ensuring that default passwords are changed immediately upon deployment.
Regular Security Audits
Conducting regular security audits is essential for identifying vulnerabilities and ensuring compliance with security standards. These audits should include assessments of both the firewall and the IoT devices themselves.
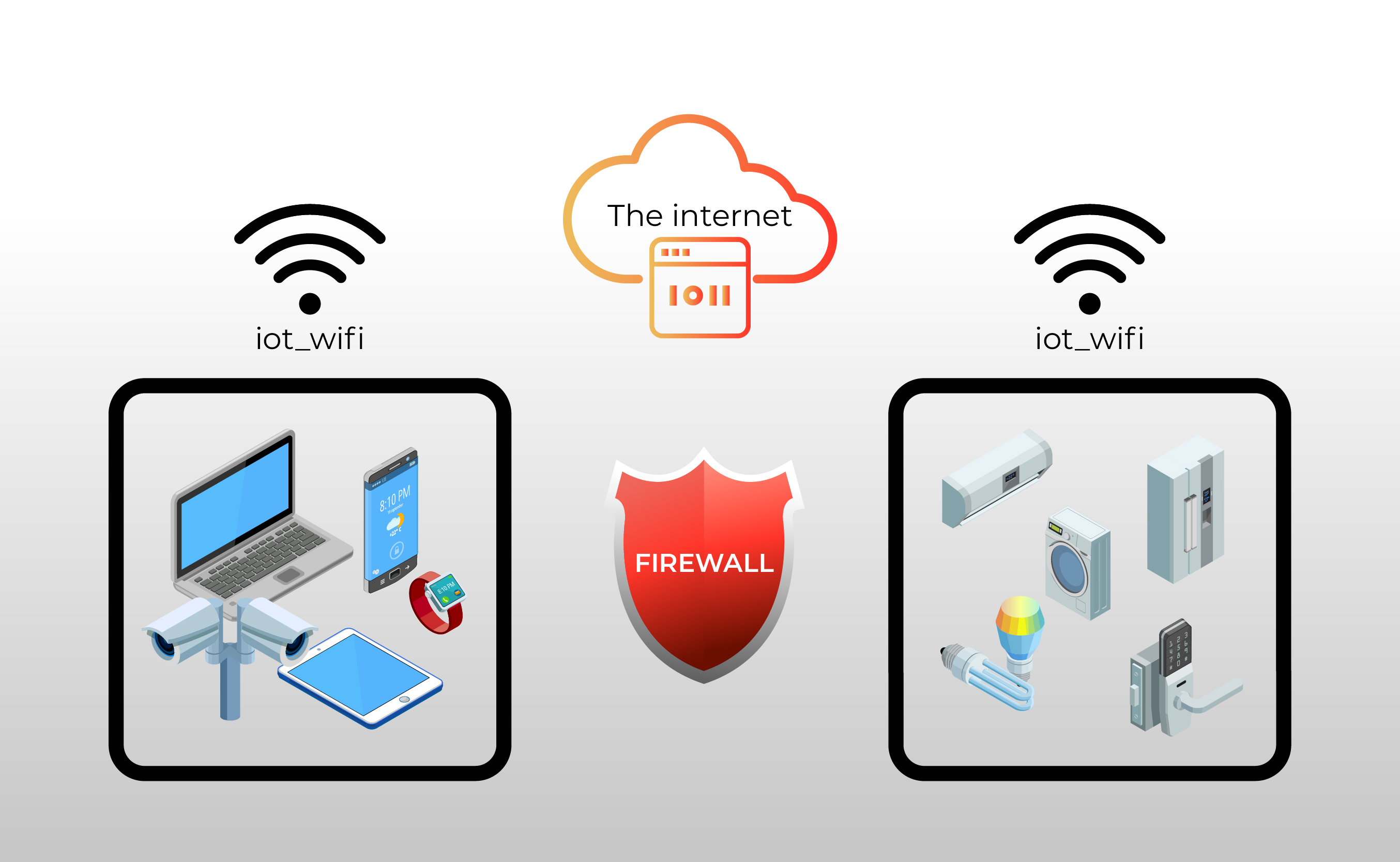
The Importance of Network Segmentation
Network segmentation is a critical strategy for managing IoT devices behind a firewall. By separating IoT devices from other parts of the network, organizations can limit the potential impact of a security breach.
Segmentation also allows for more granular control over network traffic, enabling administrators to apply specific security policies to different groups of devices.
Effective IoT Device Management
Inventory and Asset Management
Keeping an accurate inventory of all IoT devices is essential for effective management. This includes tracking device types, firmware versions, and security configurations. By maintaining a comprehensive inventory, organizations can quickly identify and address potential security issues.
Automated Management Tools
Utilizing automated management tools can significantly streamline the process of managing IoT devices. These tools can handle tasks such as firmware updates, security patches, and configuration changes, reducing the burden on IT staff.
Protecting Data in IoT Networks
Data protection is a top priority when managing IoT devices behind a firewall. Ensuring that data is encrypted both in transit and at rest is crucial for preventing unauthorized access and data breaches.
Organizations should also implement data retention policies to ensure that sensitive information is stored securely and deleted when no longer needed.
Continuous Monitoring and Threat Detection
Real-Time Monitoring
Continuous monitoring of IoT networks is essential for detecting and responding to threats in real-time. This includes monitoring network traffic, device behavior, and security logs for any suspicious activity.
Threat Intelligence Integration
Integrating threat intelligence feeds into the monitoring process can enhance the ability to detect and respond to emerging threats. By leveraging global threat intelligence, organizations can stay ahead of potential attacks.
Regular Updates and Patch Management
Keeping IoT devices and firewalls up to date with the latest security patches and firmware updates is critical for maintaining a secure network. Organizations should establish a regular update schedule and ensure that updates are applied promptly.
Automated patch management tools can help streamline this process, reducing the risk of missed updates and ensuring that all devices are protected against known vulnerabilities.
Future Trends in IoT Security
The landscape of IoT security is constantly evolving, with new technologies and strategies emerging to address the challenges of managing IoT devices behind a firewall. Some of the key trends to watch include:
- Artificial intelligence and machine learning for threat detection
- Zero-trust architecture for enhanced security
- Blockchain technology for secure data management
Conclusion and Next Steps
Effectively managing IoT devices behind a firewall requires a comprehensive approach that addresses the unique challenges of IoT security. By implementing best practices such as strong authentication, network segmentation, and continuous monitoring, organizations can significantly reduce the risk of security breaches.
We encourage readers to take action by conducting a thorough security assessment of their IoT networks and implementing the strategies outlined in this guide. Additionally, sharing this article with colleagues and exploring related resources can further enhance your understanding of IoT security.
Feel free to leave a comment or share your thoughts on how you manage IoT devices behind a firewall. Together, we can build a safer and more secure IoT ecosystem.
References:
- https://www.cisco.com/c/en/us/solutions/internet-of-things/iot-security.html
- https://www.ibm.com/topics/internet-of-things
- https://www.akamai.com/us/en/multimedia/documents/state-of-the-internet/state-of-the-internet-security-report-q2-2021.pdf